154
Chapter 9: Authentication
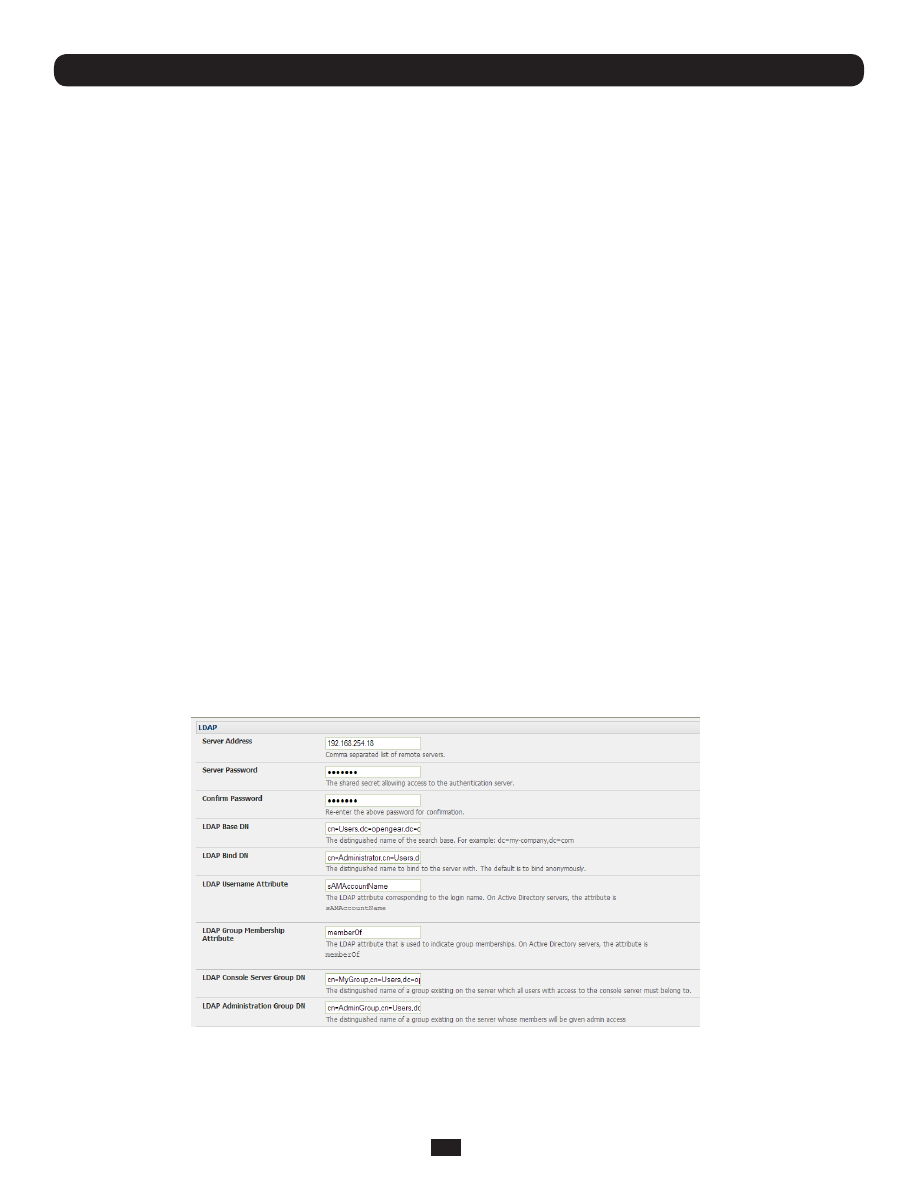
9.1.8 Remote groups with LDAP authentication
Unlike RADIUS, LDAP has built in support for group provisioning, which makes setting up remote groups easier. The console
server will retrieve a list of all the remote groups that the user is a direct member of, and compare their names with local
groups on the Console Server.
Note
: Any spaces in the group name will be converted to underscores.
For example, in an existing Active Directory setup, a group of users may be part of the “
UPS Admin
” and “
Router Admin
”
groups. On the Console Server, these users will be required to have access to a group “
Router_Admin
”, with access to port
1 (connected to the router), and another group “
UPS_Admin
”, with access to port 2 (connected to the UPS). Once LDAP is
setup, users that are members of each group will have the appropriate permissions to access the router and UPS.
Currently, the only LDAP directory service that supports group provisioning is Microsoft Active Directory. Support is planned for
OpenLDAP at a later time.
To enable group information to be used with an LDAP server:
• Complete the fields for standard LDAP authentication including LDAP Server Address, Server Password, LDAP Base DN,
LDAP Bind DN and LDAP User Name Attribute
• Enter memberOf for
LDAP Group Membership Attribute
as group membership is currently only supported on Active
Directory servers
• If required, enter the group information for
LDAP Console Server Group DN
and/or
LDAP Administration Group DN
Note:
When using remote groups with LDAP remote auth, you will need to have corresponding local groups on the console
server. In situations where LDAP group names can contain upper case and space characters, the local group name on the
console server must be all lower case and any spaces must be replaced with underscrores. For example, a remote group
on the LDAP server may be
My Ldap Access Group
, but needs a corresponding local group on the console server called
my_ldap_access_group
. For any group membership to be effective, the local group must specify what the group member is
granted access to.
A user must be a member of the LDAP Console Server Group DN group in order to gain access to the console and user
interface. For example, the user must be a member of ‘MyGroup’ on the Active Server to gain access to the Console Server.
Additionally, a user must be a member of the LDAP Administration Group DN in order to gain administrator access to the
Console Server. For example, the user must be a member of ‘AdminGroup’ on the Active Server to receive administration
privileges on the Console Server.
• Click Apply.