234
Chapter 15: Advanced Configuration
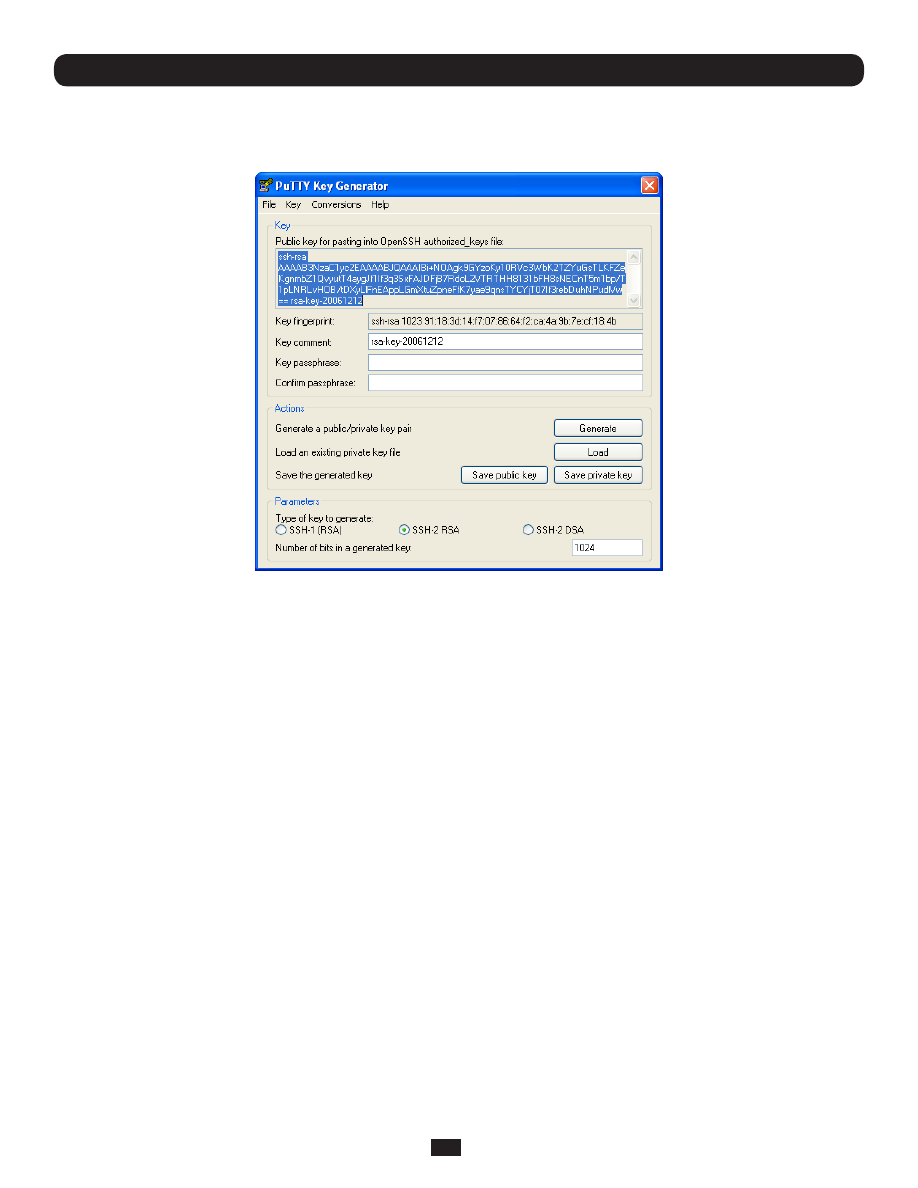
• Click on the
Generate
button
• Follow the instruction to move the mouse over the blank area of the program in order to create random data used by
PUTTYGEN to generate secure keys. Key generation will occur once PUTTYGEN has collected sufficient random data
• Create a new file " authorized_keys " (with notepad) and copy your public key data from the "Public key for pasting into
OpenSSH authorized_keys file" section of the PuTTY Key Generator, and paste the key data to the "authorized_keys" file.
Make sure there is only one line of text in this file
• Use WinSCP to copy this "authorized_keys" file into the user’s home directory: eg. /etc/config/users/testuser/.ssh/
authorized_keys of the Console Server which will be the SSH server. You will need to make sure this file is in the correct
format with the correct permissions with the following commands:
# dos2unix \
/etc/config/users/testuser/.ssh/authorized_keys && chown testuser \
/etc/config/users/testuser/.ssh/authorized_keys
• Using WinSCP copy the attached sshd_config over
/etc/config/sshd_config
on the server (Makes sure public key
authentication is enabled)
• Test the Public Key by logging in as "testuser" Test the Public Key by logging in as "testuser" to the client Console Server
device and typing (you should not need to enter anything): # ssh -o StrictHostKeyChecking=no <server-ip>
To automate connection of the SSH tunnel from the client on every power-up you need to make the clients
/etc/config/rc.local
look like the following:
#!/bin/sh
ssh -L9001:127.0.0.1:4001 -N -o StrictHostKeyChecking=no testuser@<server-ip> &
This will run the tunnel redirecting local port 9001 to the server port 4001.
15.6.6 Fingerprinting
Fingerprints
are used to ensure you are establishing an SSH session to who you think you are. On the first connection to a
remote server you will receive a fingerprint which you can use on future connections.