248
15.14.4 How it works
This section explains in detail how the Appliance uses DHCP to obtain its initial configuration.
First, an appliance is either configured or unconfigured. ZTP needs it to be in an unconfigured state, which is only obtained in
the following ways:
• Firmware programming at factory
• Pressing the Config Erase button twice during operation
• Selecting
Config Erase
under
System: Administration
in the web UI, and rebooting
• Creating the file /etc/config/.init and then rebooting (command-line)
When an unconfigured appliance boots, it performs these steps to find a configuration:
• The appliance transmits a DHCP DISCOVER request onto its primary Network Interface (wan). This DHCP request will carry
a Vendor Class Identifier of the form TrippLite/model-name (for example, TrippLite/B096-016) and its parameter request
list will include option 43 (Vendor-Specific Information).
• On receipt of a DHCP OFFER, the device will use the information in the offer to assign an IPv4 address to its primary
Network Interface, add a default route, and prepare its DNS resolver.
• If the offer also contained an option 43 with sub-option 1, the device interprets the sub-option as a whitespace-separated
list of URLs to configuration files to try to restore.
• If an NTP server option was provided in the DHCP offer, the system clock is quickly synchronized with the NTP server.
• The system now searches all attached USB storage devices for two optional certificate files. The first file is named ca-
bundle.crt and the second one is whichever one of the following filenames is found first:
o client-AABBCCDDEEFF.pem (where AABBCCDDEEFF is the MAC address of the primary network interface); or
o client-MODEL.pem (where MODEL is the (vendor class) model name in lowercase, truncated to before the first
hyphen); or
o client.pem
• If both files are found (ca-bundle.crt and a client.pem), then secure mode is enabled for the next section.
• Each URL in the list obtained from option 43 sub-option 1 is tried in sequence until one succeeds:
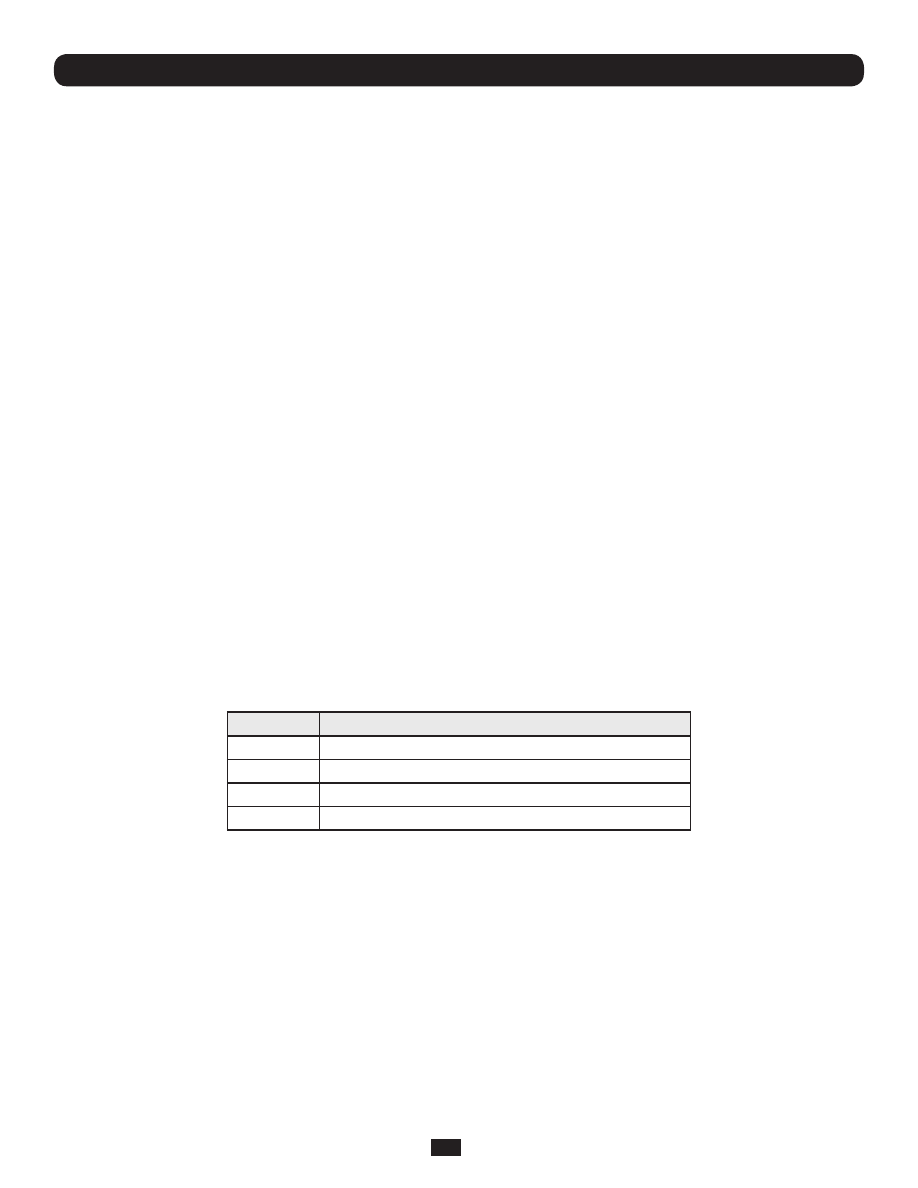
o The URL undergoes substring replacement from the following table:
Substring
Replaced by
${mac}
the 12-digit MAC address of the appliance, lowercase
${model}
the full model name, in lowercase
${class}
the firmware hardware class
${version}
the firmware version number
o The resulting URL must end in .opg or .xml (an optional ?query-string is permitted). If it doesn’t, then it is skipped and
the next URL is tried.
o In secure mode, the URL must use the https scheme or it is skipped.
o Otherwise the available schemes are: http, https, tftp, ftp, ftps
o The curl program is used to download the URL.
o In secure mode, the server’s certificate must validate against the ca-bundle.crt. The (required) client.pem file is
provided to authenticate the client to the server. Please see the curl documentation for the format of these files.
• The URL is downloaded. For .opg files its header is checked to see if it is compatible with the current appliance. For .xml
files, a parse check is made. If the check fails, the downloaded file is abandoned and the next URL is tried.
• The file is imported into the current configuration.
• The system checks to see if a hostname has been set in the config. If not, it is set to ${model}-${mac}.
Chapter 15: Advanced Configuration