226
Chapter 15: Advanced Configuration
15.5.3 Enable SNMP service
Note:
For firmware versions 3.10.2 and above, a new SNMP status and trap MIBS were created to provide more and better
structured SNMP status and traps from
console servers
. There is an option in the SNMP menu to
Use Legacy Notifications
for the SNMP traps. In setting this option, the console server will send SNMP traps that are compatible with those sent from
older firmware versions before new MIBS were added. This ensures that the firmware upgrade will not upset the existing SNMP
management settings already in place.
When upgrading from an old firmware version that does not support newer SNMP MIBs/traps (versions before 3.10.2) to
firmware that does support the new MIBs/traps:
• If the SNMP service was enabled and an SNMP manager was configured before upgrading the firmware, the console
server will be configured to use the legacy traps after upgrading.
• If the SNMP service was not enabled or no SNMP manger was configured before the upgrade, then the console server will
be configured to use the new SNMP traps after the upgrade. Note: this will not have any effect until the SNMP service is
turned on and an SNMP manager is configured.
• When starting up using the new firmware after a config erase, the console server will be configured to use the new SNMP
traps.
• When upgrading from a firmware version that supports the new traps to a newer version that supports the new traps, the
‘use legacy traps’ setting should be kept the same – no checking SNMP service/manager configuration is needed.
The Console Server supports different versions of SNMP including SNMPv1, SNMPv2c and SNMPv3.
SNMP, although an industry standard, brings with it a variety of security concerns. For example, SNMPv1 and SNMPv2c offer
no inherent privacy, while SNMPv3 is susceptible to man-in-the-middle attacks. Recent IETF developments suggests tunnelling
SNMP over widely accepted technologies such as SSH (Secure Shell) or TLS (Transport Layer Security) rather than relying on a
less mature security systems such as SNMPv3's USM (User-based Security Model).
Additional information regarding SNMP security issues and SNMPv3 can be found at:
http://net-snmp.sourceforge.net/wiki/index.php/TUT:Security
http://www.ietf.org/html.charters/snmpv3-charter.html.
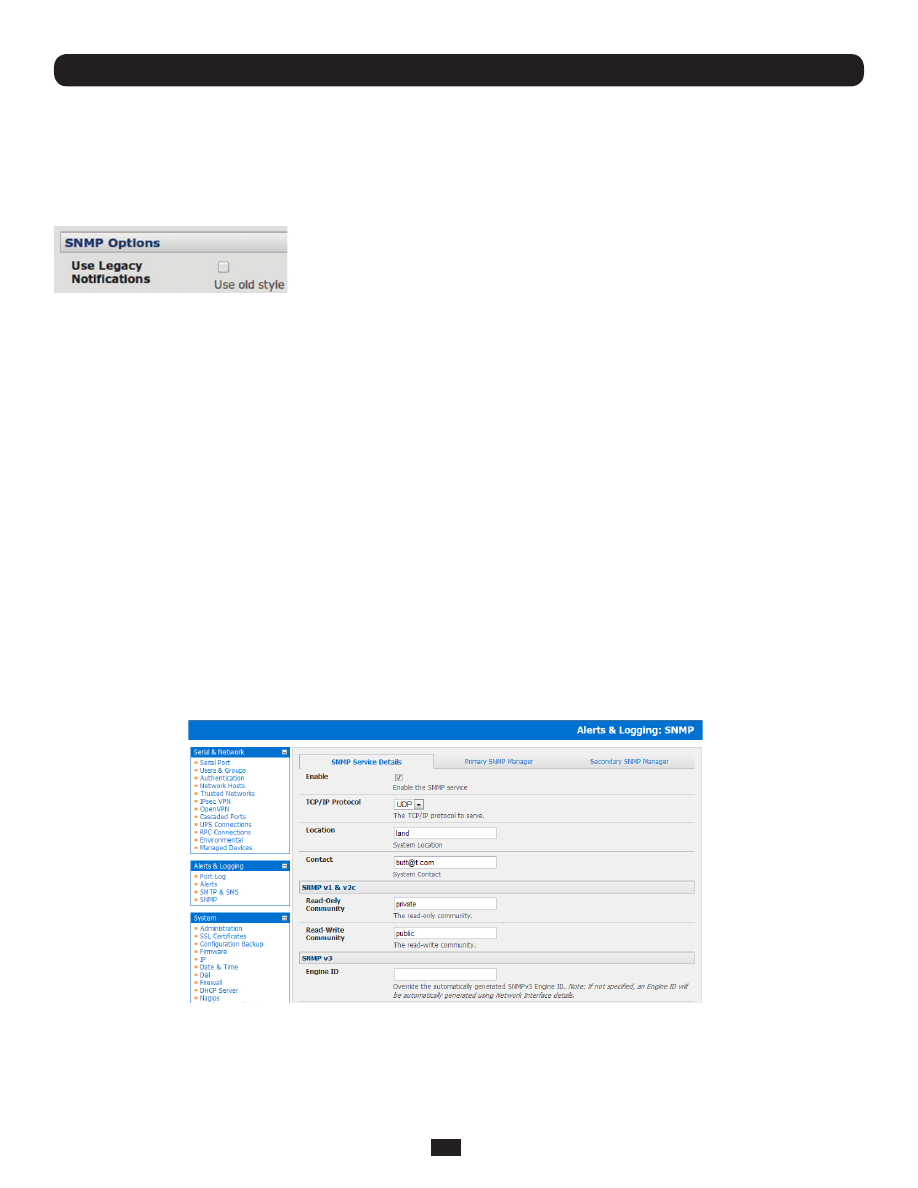
• Select
Alerts & Logging: SNMP
• The
SNMP Service Details
tab is shown by default. The SNMP Service Details tab controls aspects of the SNMP
Service including Security Level. It manages requests from external agents for status information.
• Check the
Enable the SNMP Service
box to start the SNMP Service. The Service is disabled by default.
• Select either
UDP
or
TCP
for the TCP/IP Protocol. UDP is the recommended protocol and is selected by default. TCP
should only be used in special cases such as when Port Forwarding SNMP requests/responses to or from the Console
Server device is required.