156
Chapter 9: Authentication
9.1.10 Kerberos authentication
The Kerberos authentication can be used with UNIX and Windows (Active Directory) Kerberos servers. This form of authentication
does not provide group information, so a local user with the same username must be created, and permissions set.
Note
: Kerberos is very sensitive to time differences between the Key Distribution Center (KDC) authentication server and the
client device. Please make sure that NTP is enabled, and the time zone is set correctly on the console server.
When authenticating against Active Directory, the Kerberos Realm will be the domain name, and the Master KDC will be the
address of the primary domain controller.
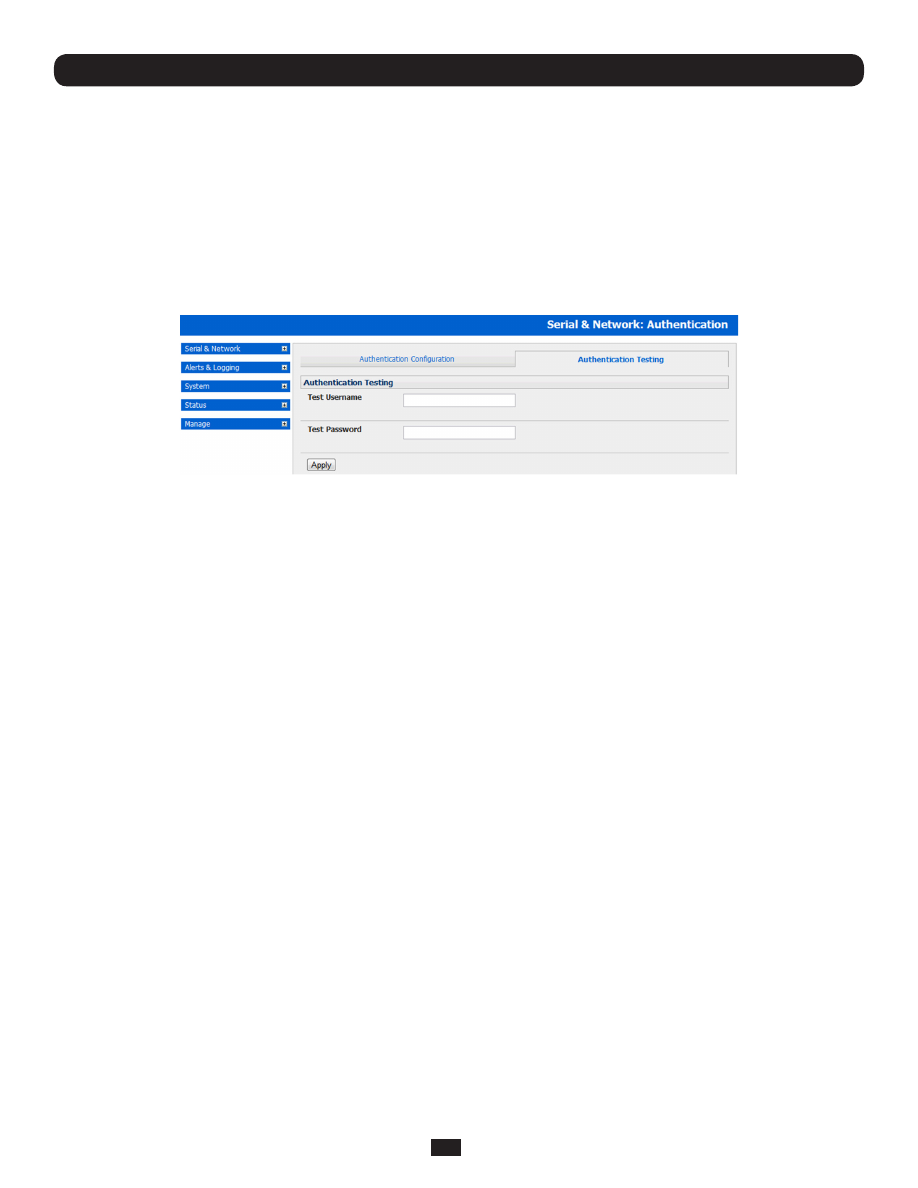
9.1.11 Authentication testing
The Authentication Testing tab enables the connection to the remote authentication server to be tested.
9.2 PAM (Pluggable Authentication Modules)
The Console Server supports RADIUS, TACACS+ and LDAP for two-factor authentication via PAM (Pluggable Authentication
Modules). PAM is a flexible mechanism for authenticating Users. Nowadays, a number of new ways of authenticating users
have become popular. The challenge is that each time a new authentication scheme is developed, it requires all the necessary
programs (login, ftpd, etc.) to be rewritten to support it.
PAM provides a way to develop programs that are independent of authentication schemes. These programs need
"authentication modules" to be attached to them at run-time in order to work. Which authentication module is to be attached
is dependent upon the local system setup and is at the discretion of the local Administrator.
The Console Server family supports PAM to which we have added the following modules for remote authentication:
RADIUS
- pam_radius_auth
(http://www.freeradius.org/pam_radius_auth/)
TACACS+
- pam_tacplus
(http://echelon.pl/pubs/pam_tacplus.html)
LDAP
- pam_ldap
(http://www.padl.com/OSS/pam_ldap.html)
Further modules can be added as required.
Changes may be made to files in /etc/config/pam.d/ which will persist, even if the authentication configurator is run.
• Users added on demand:
When a user attempts to log in, but does not already have an account on the Console Server, a new user account will be
created. This account will not have any rights, and no password set. They will not appear in the configuration tools.
Automatically added accounts will not be able to log in if the remote servers are unavailable. RADIUS users are currently
assumed to have access to all resources, so will only be authorized to log in to the Console Server. RADIUS users will be
authorized each time they access a new resource.
• Admin rights granted over AAA:
Users may be granted Administrator rights via networked AAA. For TACACS, a priv-lvl of 12 of above indicates an
administrator. For RADIUS, administrators are indicated via the Framed Filter ID. (See the example configuration files
below, for example.)
• Authorization via TACACS for both serial ports and host access:
Permission to access resources may be granted via TACACS by indicating an appliance and a port or networked host the
user may access. (See the example configuration files below, for example.)