Chapter 7 Wireless LAN
P-870H/HW Series User’s Guide
108
7.10.3.4 Encryption
Wireless networks can use encryption to protect the information that is sent in the
wireless network. Encryption is like a secret code. If you do not know the secret
code, you cannot understand the message.
The types of encryption you can choose depend on the type of authentication.
(See
for information about this.)
For example, if the wireless network has a RADIUS server, you can choose WPA
or WPA2. If users do not log in to the wireless network, you can choose no
encryption, Static WEP, WPA-PSK, or WPA2-PSK.
Usually, you should set up the strongest encryption that every device in the
wireless network supports. For example, suppose you have a wireless network
with the ZyXEL Device and you do not have a RADIUS server. Therefore, there is
no authentication. Suppose the wireless network has two devices. Device A only
supports WEP, and device B supports WEP and WPA. Therefore, you should set up
Static WEP in the wireless network.
Note: It is recommended that wireless networks use
WPA-PSK
,
WPA
, or stronger
encryption. The other types of encryption are better than none at all, but it is still
possible for unauthorized wireless devices to figure out the original information
pretty quickly.
When you select WPA2 or WPA2-PSK in your ZyXEL Device, you can also select
an option (WPA compatible) to support WPA as well. In this case, if some of the
devices support WPA and some support WPA2, you should set up WPA2-PSK or
WPA2 (depending on the type of wireless network login) and select the WPA
compatible option in the ZyXEL Device.
Many types of encryption use a key to protect the information in the wireless
network. The longer the key, the stronger the encryption. Every device in the
wireless network must have the same key.
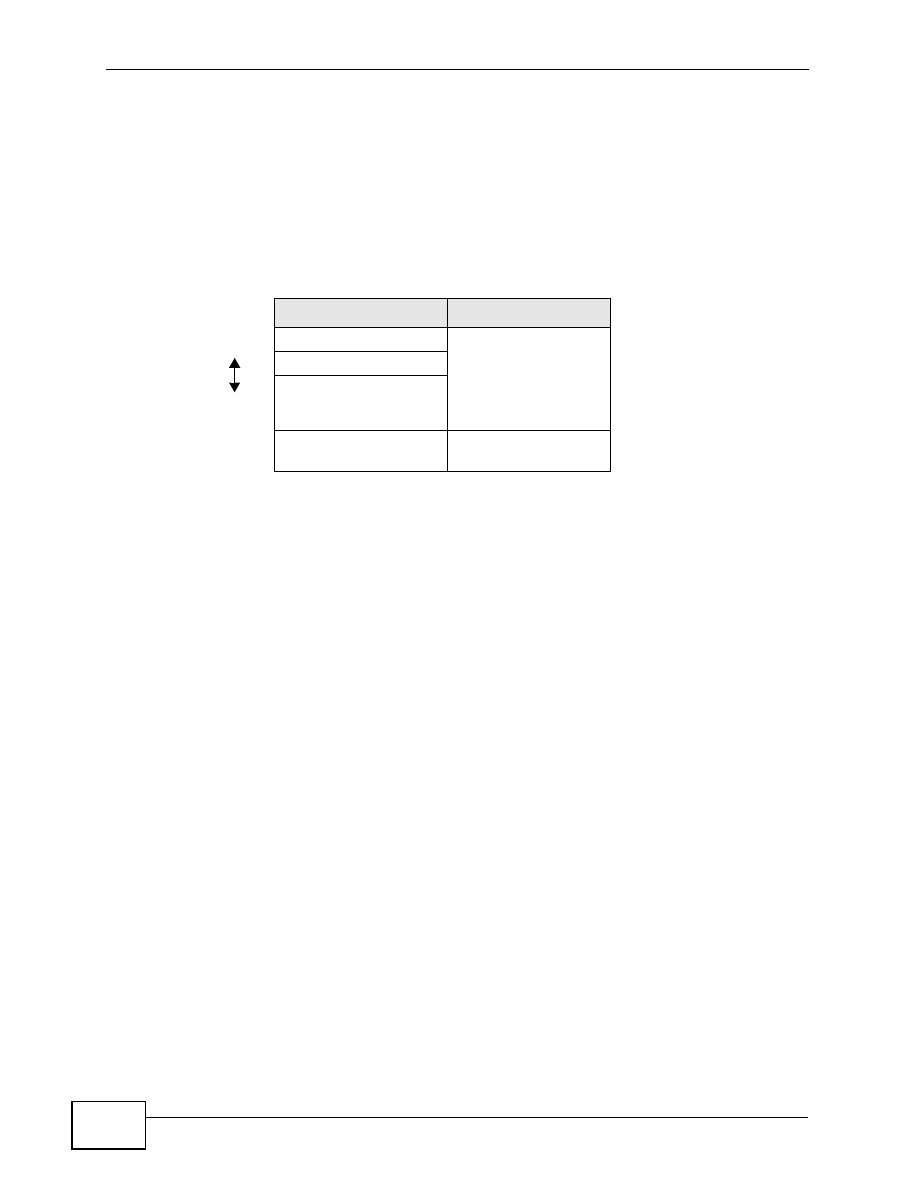
Table 34
Types of Encryption for Each Type of Authentication
NO AUTHENTICATION RADIUS SERVER
Weakest
No Security
WPA
Static WEP
WPA-PSK
Stronges
t
WPA2-PSK
WPA2