Chapter 38 Access Control
GS2210 Series User’s Guide
326
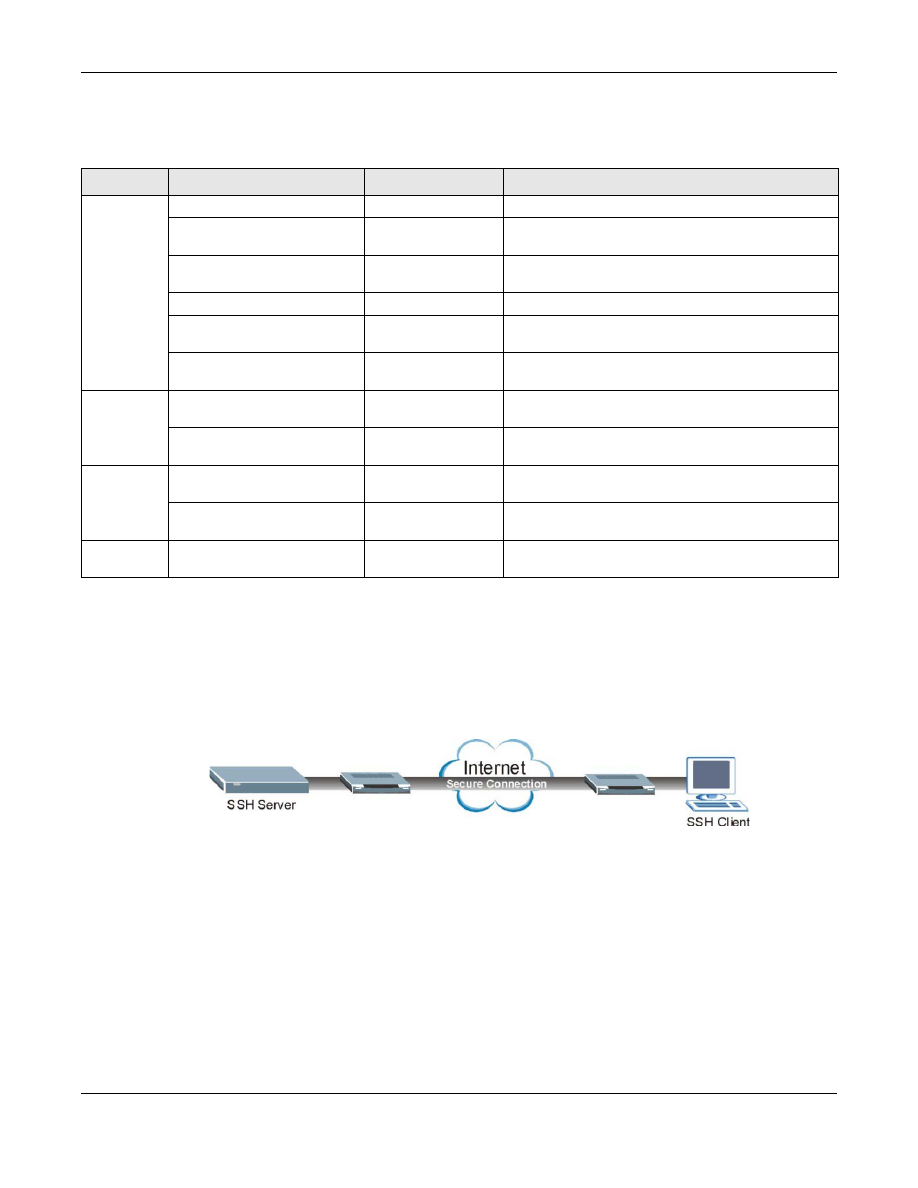
38.7.2 SSH Overview
Unlike Telnet or FTP, which transmit data in clear text, SSH (Secure Shell) is a secure
communication protocol that combines authentication and data encryption to provide secure
encrypted communication between two hosts over an unsecured network.
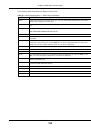
Figure 233
SSH Communication Example
38.7.2.1 How SSH works
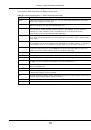
The following table summarizes how a secure connection is established between two remote hosts.
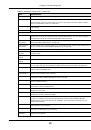
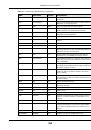
Table 163
SNMP Switch Traps
OPTION
OBJECT LABEL
OBJECT ID
DESCRIPTION
stp
STPNewRoot
1.3.6.1.2.1.17.0.1
This trap is sent when the STP root switch changes.
zyMrstpNewRoot
1.3.6.1.4.1.890.1.15
.3.52.3.1
This trap is sent when the MRSTP root switch
changes.
zyMstpNewRoot
1.3.6.1.4.1.890.1.15
.3.53.3.1
This trap is sent when the MSTP root switch changes.
STPTopologyChange
1.3.6.1.2.1.17.0.2
This trap is sent when the STP topology changes.
zyMrstpTopologyChange
1.3.6.1.4.1.890.1.15
.3.52.3.2
This trap is sent when the MRSTP topology changes.
zyMstpTopologyChange
1.3.6.1.4.1.890.1.15
.3.53.3.2
This trap is sent when the MSTP root switch changes.
mactable
zyMacForwardingTableFull
1.3.6.1.4.1.890.1.15
.3.48.2.1
This trap is sent when more than 99% of the MAC
table is used.
zyMacForwardingTableFullReco
vered
1.3.6.1.4.1.890.1.15
.3.48.2.2
This trap is sent when the MAC address switching
table has become normal from full.
rmon
RmonRisingAlarm
1.3.6.1.2.1.16.0.1
This trap is sent when a variable goes over the RMON
"rising" threshold.
RmonFallingAlarm
1.3.6.1.2.1.16.0.2
This trap is sent when the variable falls below the
RMON "falling" threshold.
cfm
dot1agCfmFaultAlarm
1.3.111.2.802.1.1.8.
0.1
The trap is sent when the Switch detects a
connectivity fault.