Chapter 19 Firewall
ZyWALL 110/310/1100 Series User’s Guide
266
Note: At the time of writing the ZyWALL’s VPN and GRE tunnels support IPv4 traffic so
IPv6 firewall rules do not apply to IPSec, SSL VPN, and GRE tunnel traffic.
To-ZyWALL Rules
Rules with ZyWALL as the To Zone apply to traffic going to the ZyWALL itself. By default:
• The firewall allows only LAN, WLAN, or WAN computers to access or manage the ZyWALL.
• The ZyWALL allows DHCP traffic from any interface to the ZyWALL.
• The ZyWALL allows DHCPv6 and Default_Allow_ICMPv6_Group traffic from any interface to the
ZyWALL.
• The ZyWALL drops most packets from the DMZ zone to the ZyWALL itself and generates a log
except for DNS and NetBIOS traffic.
• The ZyWALL drops most packets from the WLAN zone to the ZyWALL itself and generates a log
except for BOOTP_SERVER, HTTP, HTTPS, and DNS traffic.
• The ZyWALL drops most packets from the WAN zone to the ZyWALL itself and generates a log
except for AH, ESP, GRE, HTTPS, IKE, NATT (NATT applies to IPv4 only), and VRRP traffic.
When you configure a firewall rule for packets destined for the ZyWALL itself, make sure it does not
conflict with your service control rule. See
for more information about
service control (remote management). The ZyWALL checks the firewall rules before the service
control rules for traffic destined for the ZyWALL.
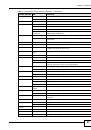
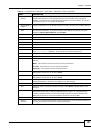
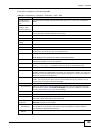
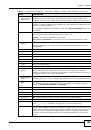
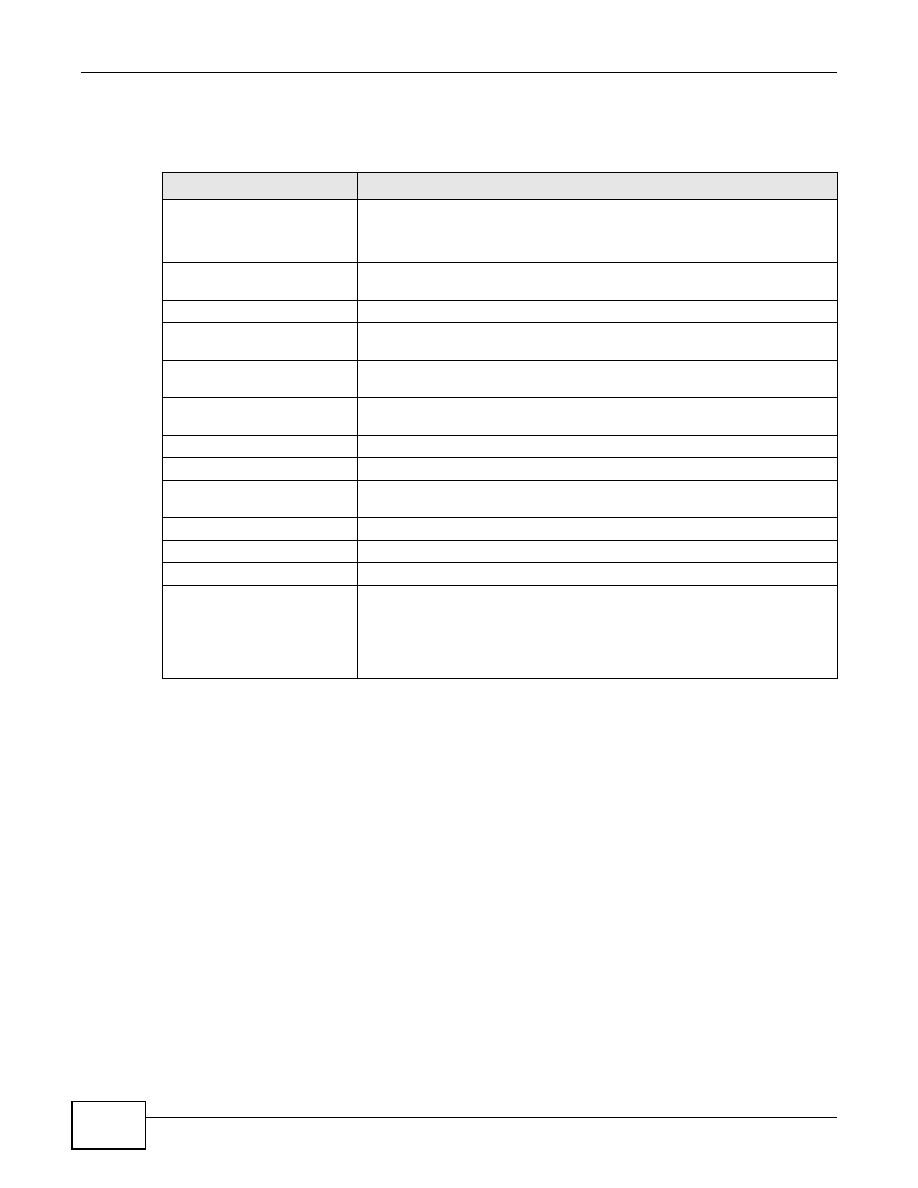
Table 97
Example Firewall Behavior
FROM ZONE TO ZONE
BEHAVIOR
From any to ZyWALL
DHCP traffic from any interface to the ZyWALL is allowed.
DHCPv6 and Default_Allow_ICMPv6_Group traffic from any interface to the
ZyWALL is allowed.
From LAN to any (other than
the ZyWALL)
Traffic from the LAN to any of the networks connected to the ZyWALL is
allowed.
From DMZ to WAN
Traffic from the DMZ to the WAN is allowed.
From IPSec VPN to any (other
than the ZyWALL)
Traffic from the IPSec VPN zone to any of the networks connected to the
ZyWALL is allowed.
From SSL VPN to any (other
than the ZyWALL)
Traffic from the SSL VPN zone to any of the networks connected to the
ZyWALL is allowed.
From TUNNEL to any (other
than the ZyWALL)
Traffic from the TUNNEL zone to any of the networks connected to the
ZyWALL is allowed.
From LAN to ZyWALL
Traffic from the LAN to the ZyWALL itself is allowed.
From DMZ to ZyWALL
DNS and NetBIOS traffic from the DMZ to the ZyWALL itself is allowed.
From WAN to ZyWALL
The default services listed in
are allowed from
the WAN to the ZyWALL itself. All other WAN to ZyWALL traffic is dropped.
From IPSec VPN to ZyWALL
Traffic from the IPSec VPN zone to the ZyWALL itself is allowed.
From SSL VPN to ZyWALL
Traffic from the SSL VPN zone to the ZyWALL itself is allowed.
From TUNNEL to ZyWALL
Traffic from the TUNNEL zone to the ZyWALL itself is allowed.
From any to any
Traffic that does not match any firewall rule is dropped. This includes traffic
from the DMZ or WAN to any of the networks behind the ZyWALL and traffic
other than DNS and NetBIOS from the DMZ to the ZyWALL.
This also includes traffic to or from interfaces or VPN tunnels that are not
assigned to a zone (extra-zone traffic).