Chapter 10: Managing the RADIUS Servers
Authorization and configuration groups
223
•
Realms
The
authfile
associates realm names with specific RADIUS Servers. Inside
the
authfile
, separate lines of printable text always begin with the name of
separate realms. After the realm name, each line also contains the special
keyword “RADIUS” (indicating that the RADIUS protocol will be used to
authenticate users associated with this realm) and then the DNS name or
IP address of a RADIUS Server where requests can be forwarded to satisfy
the authentication requirements of that realm.
The destination RADIUS server is the one whose name matches the realm
part of the username. It follows the site character. For example, in the auth
file entry “NYC RADIUS 192.168.14.23”, for the user Bob@NYC, NYC is
the realm. Packets will be forwarded to the IP address 192.168.14.23 on
the port (taken from the users file) of 1812.
It is possible to proxy to other RADIUS servers running on a different port.
To enable this, the clients file is consulted.
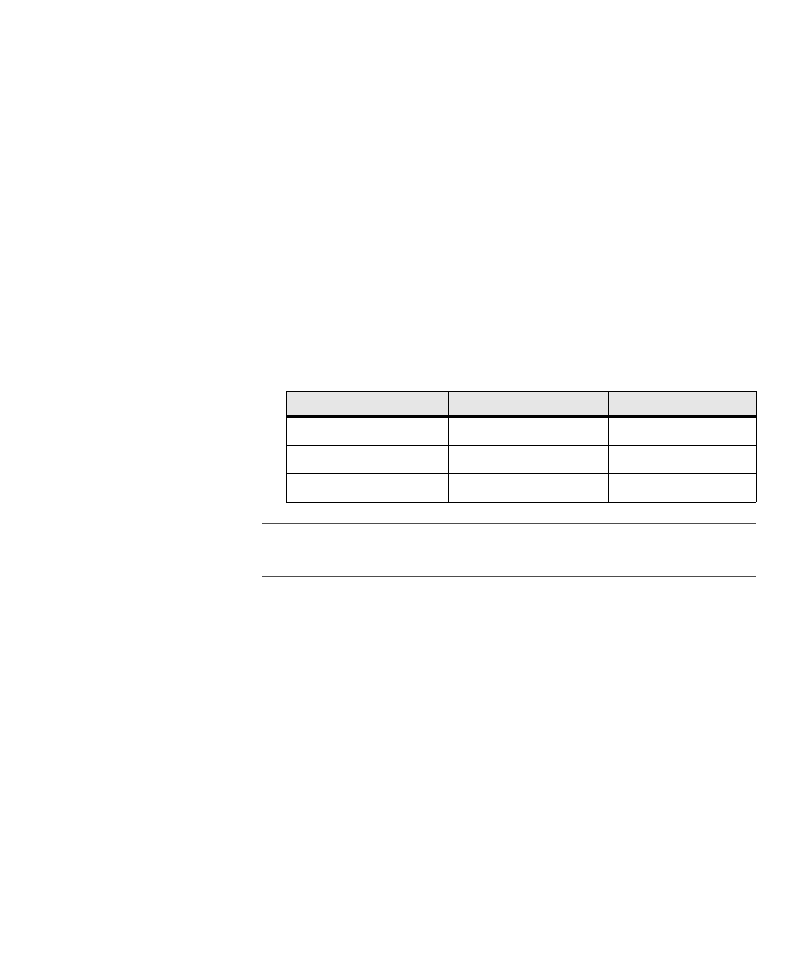
Table 14:
Sample client file entries
Note:
The Network Access Server (NAS) field of the previous table is for clients (if
one client has a NAS, all other clients must also), and PROXY is when this server
will become a “middle man” and needs to send data to another RADIUS server.
•
Server position
When RADIUS proxy forwarding is in use, each RADIUS Server can be a
member of a chain of cooperating RADIUS severs, and within that chain,
each server can perform any of three distinct roles, depending on whether
its position is first in the chain, last in the chain, or somewhere in between.
The first RADIUS Server in the chain is the only one that ever communi-
cates directly with the originating RADIUS client. The “middle” RADIUS
Servers simply forward RADIUS requests to the next member of the
chain after adding a tiny place-marker attribute to the packet. The RADIUS
Servers remove their own place marker attributes from the resulting
response packets on the return trip, before forwarding those responses
back to the next link of the chain in the opposite direction. Therefore,
although “later” links in the chain can see the place markers of earlier links,
earlier links in the chain never see any of the attributes of the later links,
and by the time the response packet arrives back at the originating RADIUS
client, all routine proxying information is removed so it can look just like a
“normal” packet that has never been forwarded.
The last link in the chain of RADIUS Servers determines that it is the last
IP [:port]
Keyword
[NAS: PROXY]
192.168.1.100
1234
NAS
192.168.14.23
MySecret
PROXY
192.168.14.23:1812
TooManySecrets
PROXY



























































































































































































































































































