Chapter 15 System
NWA3000-N Series User’s Guide
225
15.11 Technical Reference
This section provides some technical background information about the topics
covered in this chapter.
Internal RADIUS Server
PEAP (Protected EAP) and MD5 authentication is implemented on the internal
RADIUS server using simple username and password methods over a secure TLS
connection. See
Appendix D on page 323
for more information on the types of EAP
authentication and the internal RADIUS authentication method used in your
NWA3000-N series AP.
Note: The internal RADIUS server does not support domain accounts (DOMAIN/
user). When you configure your Windows XP SP2
Wireless Zero Configuration
PEAP/MS-CHAPv2 settings, clear the
Use Windows logon name and
password
check box. When authentication begins, a pop-up dialog box
requests you to type a
Name
,
Password
and
Domain
of the RADIUS server.
Specify a name and password only, do not specify a domain.
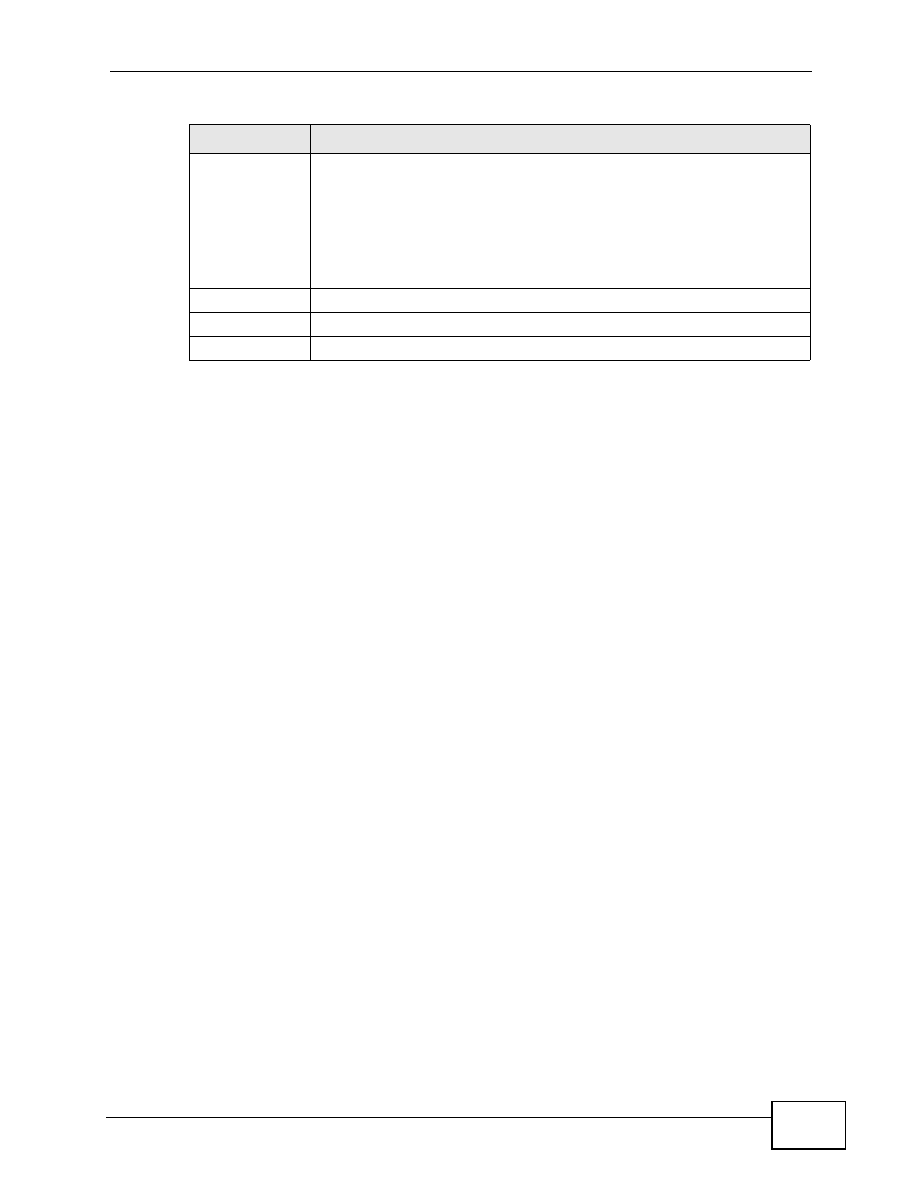
Secret
Enter a password (up to 31 alphanumeric characters, no spaces) as the
key for encrypting communications between the NWA3000-N series AP
and this entry’s AP. The key is not sent over the network. This key must
be the same on the NWA3000-N series AP and the AP.
Both the NWA3000-N series AP’s IP address and this shared secret must
also be configured in the “external RADIUS” server fields of the trusted
AP.
Description
Type some information to help identify the trusted AP.
OK
Click
OK
to
save your changes back to the NWA3000-N series AP.
Cancel
Click
Cancel
to exit this screen without saving your changes.
Table 81
Configuration > System > Auth. Server (continued)
LABEL
DESCRIPTION