Prestige 334 User’s Guide
Chapter 15 VPN Screens
166
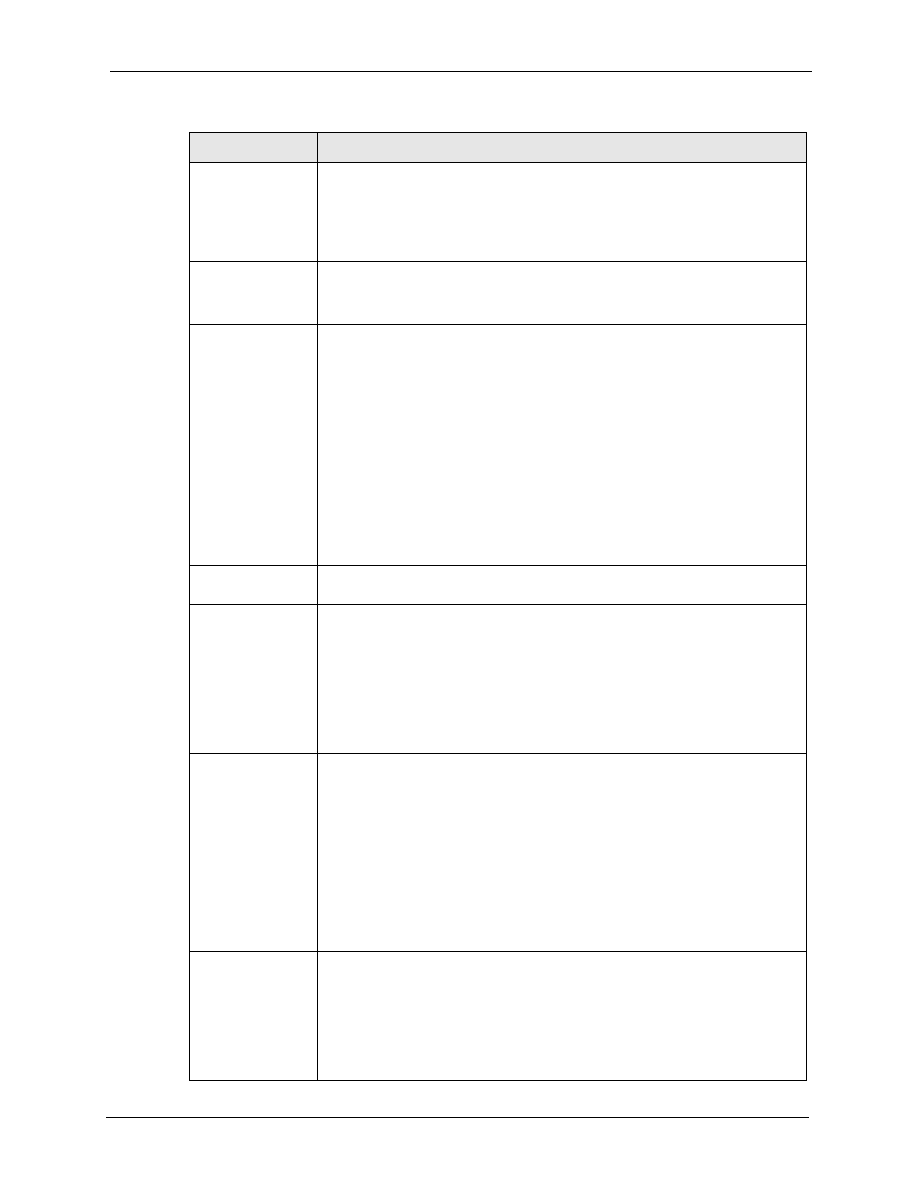
Secure Gateway
Address
Type the WAN IP address or the URL (up to 31 characters) of the IPSec router
with which you're making the VPN connection. Set this field to
0.0.0.0
if the
remote IPSec router has a dynamic WAN IP address (the
IPSec Keying Mode
field must be set to
IKE
). The remote address fields do not apply when the
Secure Gateway Address
field is configured to
0.0.0.0
. In this case only the
remote IPSec router can initiate the VPN.
Peer ID Type
Select
IP
to identify the remote IPSec router by its IP address.
Select
DNS
to identify the remote IPSec router by a domain name.
Select
to identify the remote IPSec router by an e-mail address.
Peer Content
The configuration of the peer content depends on the peer ID type.
For
IP
, type the IP address of the computer with which you will make the VPN
connection. If you configure this field to
0.0.0.0
or leave it blank, the Prestige will
use the address in the
Secure Gateway Address
field (refer to the
Secure
Gateway Address
field description).
For
DNS
or
, type a domain name or e-mail address by which to identify
the remote IPSec router. Use up to 31 ASCII characters including spaces,
although trailing spaces are truncated. The domain name or e-mail address is for
identification purposes only and can be any string.
It is recommended that you type an IP address other than
0.0.0.0
or use the
DNS
or
ID type in the following situations:
When there is a NAT router between the two IPSec routers.
When you want the Prestige to distinguish between VPN connection requests
that come in from remote IPSec routers with dynamic WAN IP addresses.
Encapsulation
Mode
Select
Tunnel
mode or
Transport
mode from the drop-down list box.
IPSec Protocol
Select
ESP
if you want to use ESP (Encapsulation Security Payload). The ESP
protocol (RFC 2406) provides encryption as well as some of the services offered
by AH. If you select
ESP
here, you must select options from the
Encryption
Algorithm
and
Authentication Algorithm
fields (described next).
Select
AH
if you want to use AH (Authentication Header Protocol). The AH
protocol (RFC 2402) was designed for integrity, authentication, sequence
integrity (replay resistance), and non-repudiation but not for confidentiality, for
which the ESP was designed. If you select
AH
here, you must select options
from the
Authentication Algorithm
field (described later).
Pre-Shared Key
Type your pre-shared key in this field. A pre-shared key identifies a
communicating party during a phase 1 IKE negotiation. It is called "pre-shared"
because you have to share it with another party before you can communicate
with them over a secure connection.
Type from 8 to 31 case-sensitive ASCII characters or from 16 to 62 hexadecimal
("0-9", "A-F") characters. You must precede a hexadecimal key with a "0x” (zero
x), which is not counted as part of the 16 to 62 character range for the key. For
example, in "0x0123456789ABCDEF", “0x” denotes that the key is hexadecimal
and “0123456789ABCDEF” is the key itself.
Both ends of the VPN tunnel must use the same pre-shared key. You will receive
a “PYLD_MALFORMED” (payload malformed) packet if the same pre-shared key
is not used on both ends
Encryption
Algorithm
Select
DES
or
3DES
from the drop-down list box. The Prestige’s encryption
algorithm should be identical to the secure remote gateway. When
DES
is used
for data communications, both sender and receiver must know the same secret
key, which can be used to encrypt and decrypt the message. The
DES
encryption algorithm uses a 56-bit key. Triple
DES
(
3DES
) is a variation on
DES
that uses a 168-bit key. As a result,
3DES
is more secure than
DES
. It also
requires more processing power, resulting in increased latency and decreased
throughput.
Table 51
VPN: Rule Setup (Basic)
LABEL
DESCRIPTION





















































































































































































































































































































































































