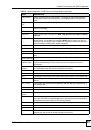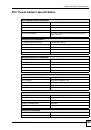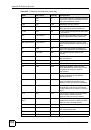
Table of Contents
ZyWALL 2WG User’s Guide
23
39.3 Configuring a Server behind NAT .................................................................................... 598
39.4 General NAT Examples ................................................................................................... 601
39.4.1 Internet Access Only .............................................................................................. 601
39.4.2 Example 2: Internet Access with a Default Server ................................................. 602
39.4.3 Example 3: Multiple Public IP Addresses With Inside Servers .............................. 603
39.4.4 Example 4: NAT Unfriendly Application Programs ................................................. 606
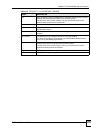
41.2.1 Configuring a Filter Rule ........................................................................................ 617
41.2.2 Configuring a TCP/IP Filter Rule ............................................................................ 618
41.2.3 Configuring a Generic Filter Rule ........................................................................... 620
41.3 Example Filter .................................................................................................................. 622
41.4 Filter Types and NAT ....................................................................................................... 624
41.5 Firewall Versus Filters ..................................................................................................... 624
41.5.1 Packet Filtering: ..................................................................................................... 624
41.5.2 Firewall ................................................................................................................... 625
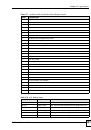
41.6.1 Applying LAN Filters ............................................................................................... 626
41.6.2 Applying DMZ Filters .............................................................................................. 626
41.6.3 Applying Remote Node Filters ............................................................................... 627
42.1 SNMP Configuration ........................................................................................................ 629
42.2 SNMP Traps .................................................................................................................... 630