ZyWALL 2WG User’s Guide
297
C
H A P T E R
15
IPSec VPN Screens
15.1 Overview
A virtual private network (VPN) provides secure communications between sites without the
expense of leased site-to-site lines. A secure VPN is a combination of tunneling, encryption,
authentication, access control and auditing. It is used to transport traffic over the Internet or
any insecure network that uses TCP/IP for communication.
Internet Protocol Security (IPSec) is a standards-based VPN that offers flexible solutions for
secure data communications across a public network like the Internet. IPSec is built around a
number of standardized cryptographic techniques to provide confidentiality, data integrity and
authentication at the IP layer.
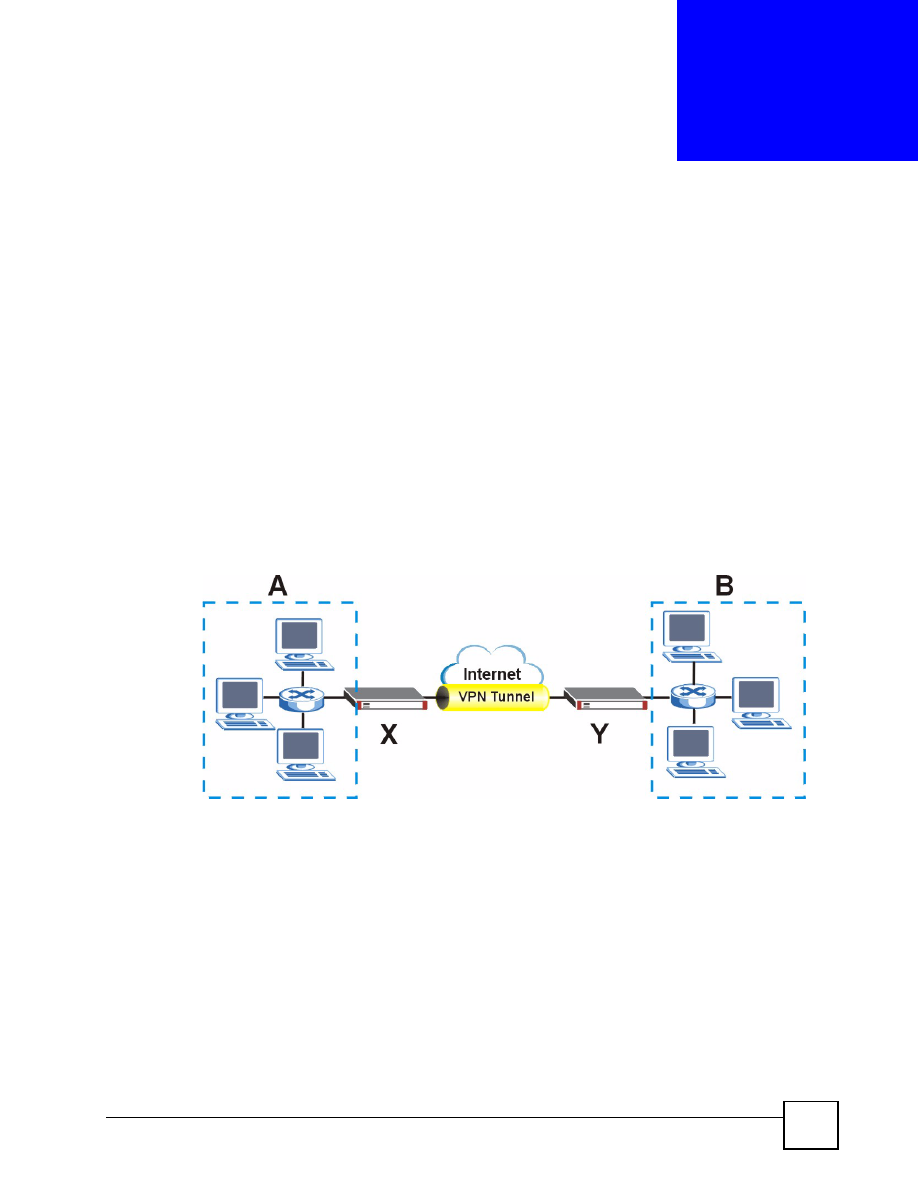
The following figure provides one perspective of a VPN tunnel.
Figure 188
VPN: Example
The VPN tunnel connects the ZyWALL (
X
) and the remote IPSec router (
Y
). These routers
then connect the local network (
A
) and remote network (
B
).
15.1.1 What You Can Do in the IPSec VPN Screens
• Use the
VPN Rules (IKE)
screens (see
) to manage the
ZyWALL’s list of VPN rules (tunnels) that use IKE SAs.
• Use the
VPN Rules (Manual)
screens (see
) to manage the
ZyWALL’s list of VPN rules (tunnels) that use manual keys. You may want to configure a
VPN rule that uses manual key management if you are having problems with IKE key
management.
• Use the
SA Monitor
screen (see
) to display and manage active
VPN connections.