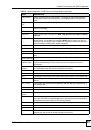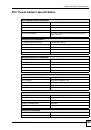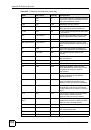
List of Figures
ZyWALL 2WG User’s Guide
29
Figure 82 SECURITY > CONTENT FILTER > Policy > External Database (Default) .......................... 133
Figure 83 HOME > DHCP Table ........................................................................................................... 134
Figure 84 SECURITY > CONTENT FILTER > Policy ........................................................................... 134
Figure 85 SECURITY > CONTENT FILTER > Policy > Insert .............................................................. 135
Figure 86 SECURITY > CONTENT FILTER > Policy ........................................................................... 135
Figure 87 SECURITY > CONTENT FILTER > Policy > Schedule (Bob) .............................................. 136
Figure 88 SECURITY > CONTENT FILTER > Policy ........................................................................... 137
Figure 89 SECURITY > CONTENT FILTER > Policy > External Database (Bob) ............................... 137
Figure 90 REGISTRATION > Registration ........................................................................................... 140
Figure 91 REGISTRATION: Registered Device ................................................................................... 141
Figure 92 REGISTRATION > Service ................................................................................................... 142
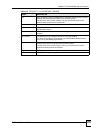
Figure 93 LAN and WAN ..................................................................................................................... 145
Figure 94 NETWORK > LAN ................................................................................................................ 149
Figure 95 NETWORK > LAN > Static DHCP ........................................................................................ 152
Figure 96 Physical Network & Partitioned Logical Networks ................................................................ 153
Figure 97 NETWORK > LAN > IP Alias ................................................................................................ 153
Figure 98 NETWORK > LAN > Port Roles ........................................................................................... 155
Figure 99 Port Roles Change Complete ............................................................................................... 155
Figure 100 Bridge Mode ....................................................................................................................... 157
Figure 101 Router Mode ....................................................................................................................... 157
Figure 102 Bridge Loop: Bridge Connected to Wired LAN ................................................................... 158
Figure 103 NETWORK > BRIDGE ....................................................................................................... 159
Figure 104 NETWORK > Bridge > Port Roles ...................................................................................... 161
Figure 105 Port Roles Change Complete ............................................................................................. 161
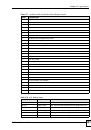
Figure 106 WAN Overview ................................................................................................................... 165
Figure 107 Different WAN IP Addresses ............................................................................................. 168
Figure 108 NETWORK > WAN > General ........................................................................................... 170
Figure 109 Least Load First Example .................................................................................................. 173
Figure 110 Load Balancing: Least Load First ....................................................................................... 174
Figure 111 Weighted Round Robin Algorithm Example ........................................................................ 175
Figure 112 Load Balancing: Weighted Round Robin ............................................................................ 176
Figure 113 Spillover Algorithm Example ............................................................................................... 177
Figure 114 Load Balancing: Spillover ................................................................................................... 177
Figure 115 NETWORK > WAN > WAN 1 (Ethernet Encapsulation) .................................................. 180
Figure 116 NETWORK > WAN > WAN 1 (PPPoE Encapsulation) ...................................................... 183
Figure 117 NETWORK > WAN > WAN 1 (PPTP Encapsulation) ........................................................ 186
Figure 118 NETWORK > WAN > 3G (WAN 2) ................................................................................... 190
Figure 119 Traffic Redirect WAN Setup ................................................................................................ 193
Figure 120 Traffic Redirect LAN Setup ................................................................................................. 194
Figure 121 NETWORK > WAN > Traffic Redirect ................................................................................ 194
Figure 122 NETWORK > WAN > Dial Backup ................................................................................... 195
Figure 123 NETWORK > WAN > Dial Backup > Edit ......................................................................... 198
Figure 124 DMZ Overview .................................................................................................................... 201