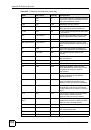
List of Tables
ZyWALL 2WG User’s Guide
42
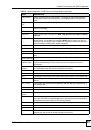
Table 39 NETWORK > WAN > WAN 1 (PPPoE Encapsulation) ......................................................... 183
Table 40 NETWORK > WAN > WAN 1 (PPTP Encapsulation) ............................................................ 186
Table 41 NETWORK > WAN > 3G (WAN 2) ........................................................................................ 190
Table 42 NETWORK > WAN > Traffic Redirect ................................................................................... 194
Table 43 NETWORK > WAN > Dial Backup ........................................................................................ 195
Table 44 NETWORK > WAN > Dial Backup > Edit .............................................................................. 199
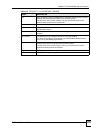
Table 45 2G, 2.5G, 2.75G, 3G and 3.5G Wireless Technologies ......................................................... 200
Table 46 NETWORK > DMZ ................................................................................................................ 205
Table 47 NETWORK > DMZ > Static DHCP ........................................................................................ 208
Table 48 NETWORK > DMZ > IP Alias ............................................................................................... 209
Table 49 NETWORK > DMZ > Port Roles ............................................................................................211
Table 50 NETWORK > WLAN ............................................................................................................. 215
Table 51 NETWORK > WLAN > Static DHCP ..................................................................................... 218
Table 52 NETWORK > WLAN > IP Alias ............................................................................................. 219
Table 53 NETWORK > WLAN > Port Roles ........................................................................................ 222
Table 54 Types of Encryption for Each Type of Authentication ........................................................... 224
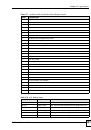
Table 55 WIRELESS > Wi-Fi > Wireless Card .................................................................................... 226
Table 56 WIRELESS > Wi-Fi > Wireless Card: SSID Profile ............................................................... 229
Table 57 Security Modes ..................................................................................................................... 229
Table 58 WIRELESS > Wi-Fi > Security .............................................................................................. 230
Table 59 WIRELESS > Wi-Fi > Security: None ................................................................................... 231
Table 60 WIRELESS > Wi-Fi > Security: WEP .................................................................................... 232
Table 61 WIRELESS > Wi-Fi > Security: 802.1x Only ......................................................................... 233
Table 62 WIRELESS > Wi-Fi > Security: 802.1x + Static WEP ........................................................... 234
Table 63 WIRELESS > Wi-Fi > Security: WPA, WPA2 or WPA2-MIX ................................................. 235
Table 64 WIRELESS > Wi-Fi > Security: WPA(2)-PSK ....................................................................... 236
Table 65 WIRELESS > Wi-Fi > MAC Filter .......................................................................................... 238
Table 66 Blocking All LAN to WAN IRC Traffic Example ..................................................................... 243
Table 67 Limited LAN to WAN IRC Traffic Example ............................................................................ 244
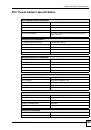
Table 68 SECURITY > FIREWALL > Default Rule (Router Mode) ...................................................... 245
Table 69 SECURITY > FIREWALL > Default Rule (Bridge Mode) ...................................................... 247
Table 70 SECURITY > FIREWALL > Rule Summary .......................................................................... 249
Table 71 SECURITY > FIREWALL > Rule Summary > Edit ................................................................ 252
Table 72 SECURITY > FIREWALL > Anti-Probing .............................................................................. 254
Table 73 SECURITY > FIREWALL > Threshold .................................................................................. 255
Table 74 SECURITY > FIREWALL > Service ...................................................................................... 256
Table 75 SECURITY > FIREWALL > Service > Add ........................................................................... 257
Table 76 SECURITY > CONTENT FILTER > General ........................................................................ 269
Table 77 SECURITY > CONTENT FILTER > Policy ........................................................................... 272
Table 78 SECURITY > CONTENT FILTER > Policy > General ........................................................... 273
Table 79 SECURITY > CONTENT FILTER > Policy > External Database .......................................... 275
Table 80 SECURITY > CONTENT FILTER > Policy > Customization ................................................. 282
Table 81 SECURITY > CONTENT FILTER > Policy > Schedule ........................................................ 284