Chapter 15 IPSec VPN Screens
ZyWALL 2WG User’s Guide
339
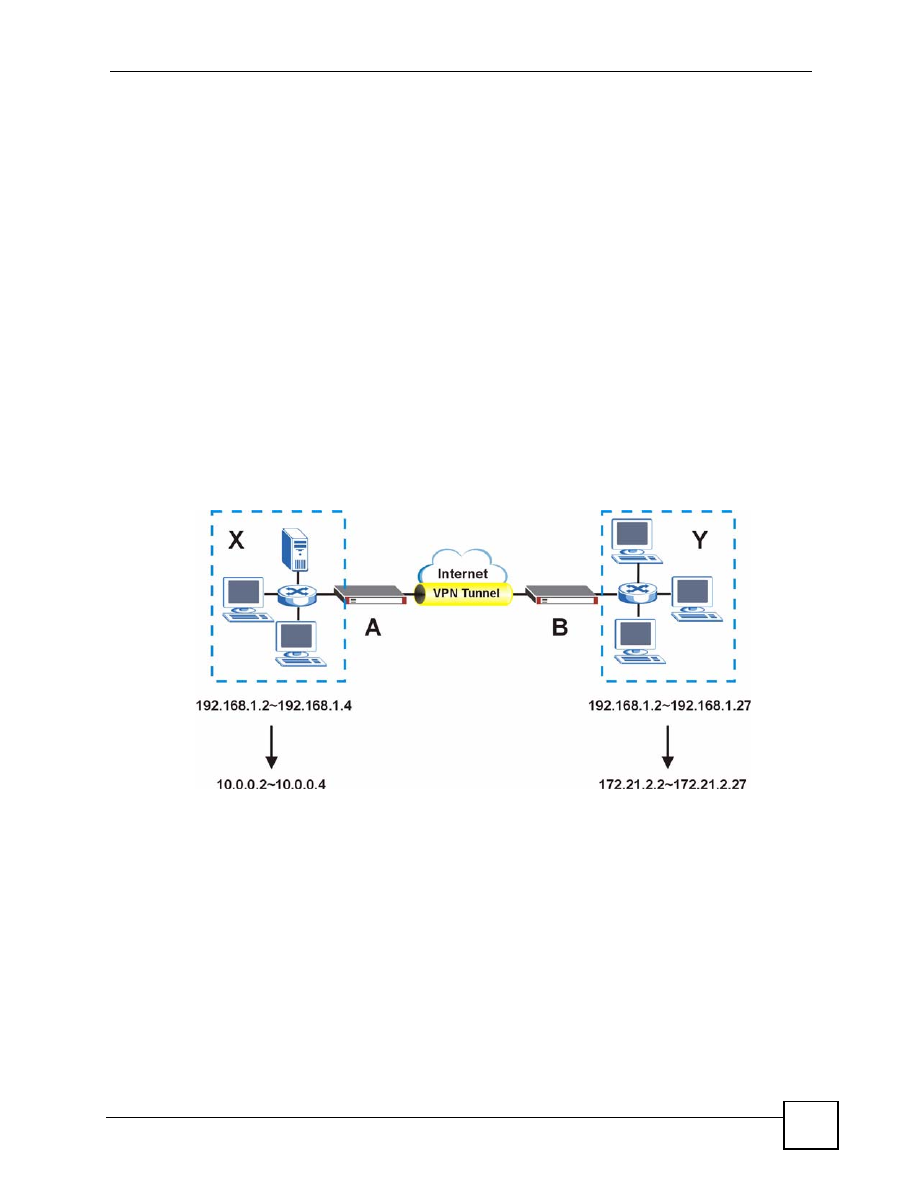
Avoiding Overlapping Local And Remote Network IP Addresses
If both IPSec routers support virtual address mapping, you can access devices on both
networks, even if their IP addresses overlap. You map the ZyWALL’s local network addresses
to virtual IP addresses and map the remote IPSec router’s local IP addresses to other (non-
overlapping) virtual IP addresses.
The following diagram shows an example of using virutal address mapping to avoid
overlapping local and remote IP addresses. You can set up virtual address mapping on both
IPSec routers to allow computers on network
X
to access network
X
and network
Y
computers
with the same IP address.
• You set ZyWALL
A
to change the source IP addresses of packets from local network
X
(192.168.1.2 to 192.168.1.4) to virtual IP addresses 10.0.0.2 to 10.0.0.4 before sending
them through the VPN tunnel.
• You set ZyWALL
B
to change the source IP addresses of packets from the remote network
Y
(192.168.1.2 to 192.168.1.27) to virtual IP addresses 172.21.2.2 to 172.21.2.27 before
sending them through the VPN tunnel.
• On ZyWALL
A
, you specify 172.21.2.2 to 172.21.2.27 as the remote network. On
ZyWALL
B
, you specify 10.0.0.2 to 10.0.0.4 as the remote network.
Figure 218
Virtual Mapping of Local and Remote Network IP Addresses
Computers on network
X
use IP addresses 192.168.1.2 to 192.168.1.4 to access local network
devices and IP addresses 172.21.2.2 to 172.21.2.27 to access the remote network devices.
Computers on network
Y
use IP addresses 192.168.1.2 to 192.168.1.27 to access local
network devices and IP addresses 10.0.0.2 to 10.0.0.4 to access the remote network devices.
Active Protocol
The active protocol controls the format of each packet. It also specifies how much of each
packet is protected by the encryption and authentication algorithms. IPSec VPN includes two
active protocols, AH (Authentication Header, RFC 2402) and ESP (Encapsulating Security
Payload, RFC 2406).