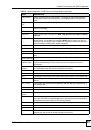
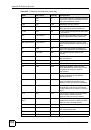
List of Tables
ZyWALL 2WG User’s Guide
43
Table 82 SECURITY > CONTENT FILTER > Object ........................................................................... 286
Table 83 SECURITY > CONTENT FILTER > Cache ........................................................................... 288
Table 84 SECURITY > VPN > VPN Rules (IKE) ................................................................................. 300
Table 85 SECURITY > VPN > VPN Rules (IKE) > Edit Gateway Policy ............................................. 303
Table 86 SECURITY > VPN > VPN Rules (IKE) > Edit Network Policy .............................................. 309
Table 87 SECURITY > VPN > VPN Rules (IKE) > Edit Network Policy > Port Forwarding ................. 313
Table 88 SECURITY > VPN > VPN Rules (IKE) > Move Network Policy ............................................ 314
Table 89 SECURITY > VPN > VPN Rules (Manual) ........................................................................... 316
Table 90 SECURITY > VPN > VPN Rules (Manual) > Edit ................................................................. 318
Table 91 SECURITY > VPN > SA Monitor .......................................................................................... 321
Table 92 SECURITY > VPN > Global Setting ...................................................................................... 323
Table 93 Telecommuters Sharing One VPN Rule Example ................................................................. 325
Table 94 Telecommuters Using Unique VPN Rules Example ............................................................. 326
Table 95 VPN Example: Matching ID Type and Content ..................................................................... 333
Table 96 VPN Example: Mismatching ID Type and Content ............................................................... 334
Table 97 SECURITY > CERTIFICATES > My Certificates .................................................................. 346
Table 98 SECURITY > CERTIFICATES > My Certificates > Details ................................................... 348
Table 99 SECURITY > CERTIFICATES > My Certificates > Export .................................................... 350
Table 100 SECURITY > CERTIFICATES > My Certificates > Import .................................................. 352
Table 101 SECURITY > CERTIFICATES > My Certificates > Import: PKCS#12 ................................ 352
Table 102 SECURITY > CERTIFICATES > My Certificates > Create ................................................. 354
Table 103 SECURITY > CERTIFICATES > Trusted CAs .................................................................... 358
Table 104 SECURITY > CERTIFICATES > Trusted CAs > Details ..................................................... 360
Table 105 SECURITY > CERTIFICATES > Trusted CAs Import ......................................................... 363
Table 106 SECURITY > CERTIFICATES > Trusted Remote Hosts .................................................... 364
Table 107 SECURITY > CERTIFICATES > Trusted Remote Hosts > Import ...................................... 365
Table 108 SECURITY > CERTIFICATES > Trusted Remote Hosts > Details ..................................... 367
Table 109 SECURITY > CERTIFICATES > Directory Servers ............................................................ 369
Table 110 SECURITY > CERTIFICATES > Directory Server > Add .................................................... 370
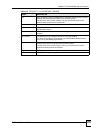
Table 111 SECURITY > AUTH SERVER > Local User Database ....................................................... 374
Table 112 SECURITY > AUTH SERVER > RADIUS ........................................................................... 374
Table 113 NAT Mapping Types ............................................................................................................ 380
Table 114 ADVANCED > NAT > NAT Overview .................................................................................. 381
Table 115 ADVANCED > NAT > Address Mapping ............................................................................. 383
Table 116 ADVANCED > NAT > Address Mapping > Edit ................................................................... 385
Table 117 ADVANCED > NAT > Port Forwarding ................................................................................ 388
Table 118 ADVANCED > NAT > Port Triggering .................................................................................. 390
Table 119 ADVANCED > STATIC ROUTE > IP Static Route ............................................................... 397
Table 120 ADVANCED > STATIC ROUTE > IP Static Route > Edit .................................................... 397
Table 121 ADVANCED > POLICY ROUTE > Policy Route Summary ................................................. 401
Table 122 ADVANCED > POLICY ROUTE > Edit ............................................................................... 403
Table 123 Application and Subnet-based Bandwidth Management Example ..................................... 409
Table 124 Over Allotment of Bandwidth Example ............................................................................... 410