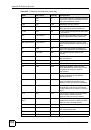
List of Figures
ZyWALL 2WG User’s Guide
30
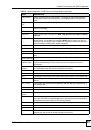
Figure 125 DMZ Public Address Example ............................................................................................ 203
Figure 126 DMZ Private and Public Address Example ........................................................................ 204
Figure 127 NETWORK > DMZ ............................................................................................................ 205
Figure 128 NETWORK > DMZ > Static DHCP ................................................................................... 208
Figure 129 NETWORK > DMZ > IP Alias ............................................................................................ 209
Figure 130 NETWORK > DMZ > Port Roles ........................................................................................211
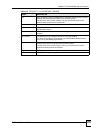
Figure 131 WLAN Overview ................................................................................................................. 213
Figure 132 NETWORK > WLAN .......................................................................................................... 215
Figure 133 NETWORK > WLAN > Static DHCP ................................................................................. 218
Figure 134 NETWORK > WLAN > IP Alias ......................................................................................... 219
Figure 135 WLAN Port Role Example ................................................................................................. 221
Figure 136 NETWORK > WLAN > Port Roles ..................................................................................... 222
Figure 137 NETWORK > WLAN > Port Roles: Change Complete ....................................................... 222
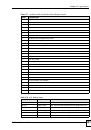
Figure 138 WIRELESS > Wi-Fi > Wireless Card ................................................................................ 226
Figure 139 WIRELESS > Wi-Fi > Wireless Card: SSID Profile ............................................................ 228
Figure 140 WIRELESS > Wi-Fi > Security ........................................................................................... 230
Figure 141 WIRELESS > Wi-Fi > Security: None ................................................................................. 231
Figure 142 WIRELESS > Wi-Fi > Security: WEP ................................................................................. 232
Figure 143 WIRELESS > Wi-Fi > Security: 802.1x Only ..................................................................... 233
Figure 144 WIRELESS > Wi-Fi > Security: 802.1x + Static WEP ........................................................ 234
Figure 145 WIRELESS > Wi-Fi > Security: WPA, WPA2 or WPA2-MIX .............................................. 235
Figure 146 WIRELESS > Wi-Fi > Security: WPA(2)-PSK ..................................................................... 236
Figure 147 NETWORK > WIRELESS CARD > MAC Filter .................................................................. 237
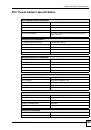
Figure 148 Default Firewall Action ........................................................................................................ 241
Figure 149 Blocking All LAN to WAN IRC Traffic Example .................................................................. 243
Figure 150 Limited LAN to WAN IRC Traffic Example .......................................................................... 244
Figure 151 SECURITY > FIREWALL > Default Rule (Router Mode) ................................................... 245
Figure 152 SECURITY > FIREWALL > Default Rule (Bridge Mode) .................................................... 247
Figure 153 SECURITY > FIREWALL > Rule Summary ....................................................................... 249
Figure 154 SECURITY > FIREWALL > Rule Summary > Edit ............................................................ 251
Figure 155 SECURITY > FIREWALL > Anti-Probing ........................................................................... 253
Figure 156 SECURITY > FIREWALL > Threshold .............................................................................. 254
Figure 157 SECURITY > FIREWALL > Service ................................................................................... 256
Figure 158 Firewall Edit Custom Service ............................................................................................. 257
Figure 159 My Service Firewall Rule Example: Service ...................................................................... 258
Figure 160 My Service Firewall Rule Example: Edit Custom Service ................................................. 258
Figure 161 My Service Firewall Rule Example: Rule Summary ........................................................... 259
Figure 162 My Service Firewall Rule Example: Rule Edit: Source and Destination Addresses .......... 259
Figure 163 My Service Firewall Rule Example: Edit Rule: Service Configuration ................................ 260
Figure 164 My Service Firewall Rule Example: Rule Summary: Completed ........................................ 261
Figure 165 From LAN to VPN Example ............................................................................................... 263
Figure 166 From VPN to LAN Example ............................................................................................... 263
Figure 167 From VPN to VPN Example .............................................................................................. 264