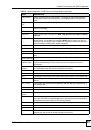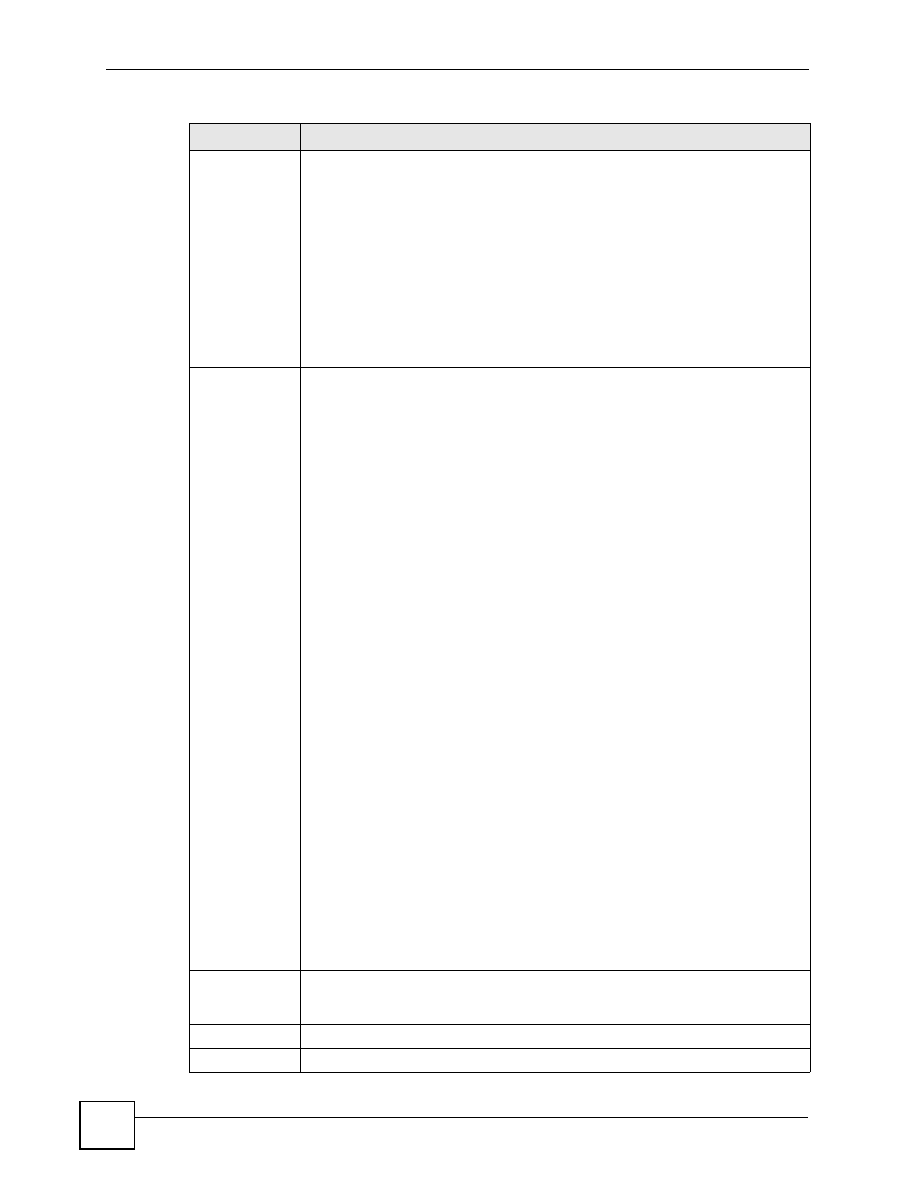
Chapter 12 Firewall Screens
ZyWALL 2WG User’s Guide
246
Allow
Asymmetrical
Route
If an alternate gateway on the LAN has an IP address in the same subnet as the
ZyWALL’s LAN IP address, return traffic may not go through the ZyWALL. This is
called an asymmetrical or “triangle” route. This causes the ZyWALL to reset the
connection, as the connection has not been acknowledged.
Select this check box to have the ZyWALL permit the use of asymmetrical route
topology on the network (not reset the connection).
Note: Allowing asymmetrical routes may let traffic from the WAN go
directly to the LAN without passing through the ZyWALL. A
better solution is to use IP alias to put the ZyWALL and the
backup gateway on separate subnets. See
Asymmetrical
Routes and IP Alias on page 264
for an example.
From, To
The firewall rules are grouped by the direction of packet travel. This displays the
number of rules for each packet direction. Click the edit icon to go to a summary
screen of the rules for that packet direction.
Here are some example descriptions of the directions of travel.
From
LAN To LAN
means packets traveling from a computer on one LAN subnet to
a computer on another LAN subnet on the LAN interface of the ZyWALL or the
ZyWALL itself. The ZyWALL does not apply the firewall to packets traveling from a
LAN computer to another LAN computer on the same subnet.
From VPN
means traffic that came into the ZyWALL through a VPN tunnel and is
going to the selected “to” interface. For example,
From VPN To LAN
specifies the
VPN traffic that is going to the LAN. The ZyWALL applies the firewall to the traffic
after decrypting it.
To VPN
is traffic that comes in through the selected “from” interface and goes out
through any VPN tunnel. For example,
From LAN To VPN
specifies the traffic that
is coming from the LAN and going out through a VPN tunnel. The ZyWALL applies
the firewall to the traffic before encrypting it.
From VPN To VPN
means traffic that comes in through a VPN tunnel and goes out
through (another) VPN tunnel or terminates at the ZyWALL. This is the case when
the ZyWALL is the hub in a hub-and-spoke VPN. This is also the case if you allow
someone to use a service (like Telnet or HTTP) through a VPN tunnel to manage the
ZyWALL. The ZyWALL applies the firewall to the traffic after decrypting it.
Note: The VPN connection directions apply to the traffic going to or
from the ZyWALL’s VPN tunnels. They do not apply to other
VPN traffic for which the ZyWALL is not one of the gateways
(VPN pass-through traffic).
Use the drop-down list box to set the firewall’s default actions based on the direction
of travel of packets.
Select
Drop
to silently discard the packets without sending a TCP reset packet or an
ICMP destination-unreachable message to the sender.
Select
Reject
to deny the packets and send a TCP reset packet (for a TCP packet)
or an ICMP destination-unreachable message (for a UDP packet) to the sender.
Select
Permit
to allow the passage of the packets.
The firewall rules for the WAN port with a higher route priority also apply to the dial
backup connection.
Log
Select the check box next to a direction of packet travel to create a log when the
above action is taken for packets that are traveling in that direction and do not match
any of your customized rules.
Apply
Click
Apply
to save your changes back to the ZyWALL.
Reset
Click
Reset
to begin configuring this screen afresh.
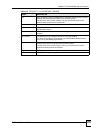
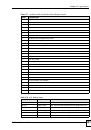
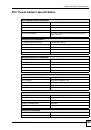
Table 68
SECURITY > FIREWALL > Default Rule (Router Mode) (continued)
LABEL
DESCRIPTION