Chapter 17 Captive Portal
NXC5200 User’s Guide
241
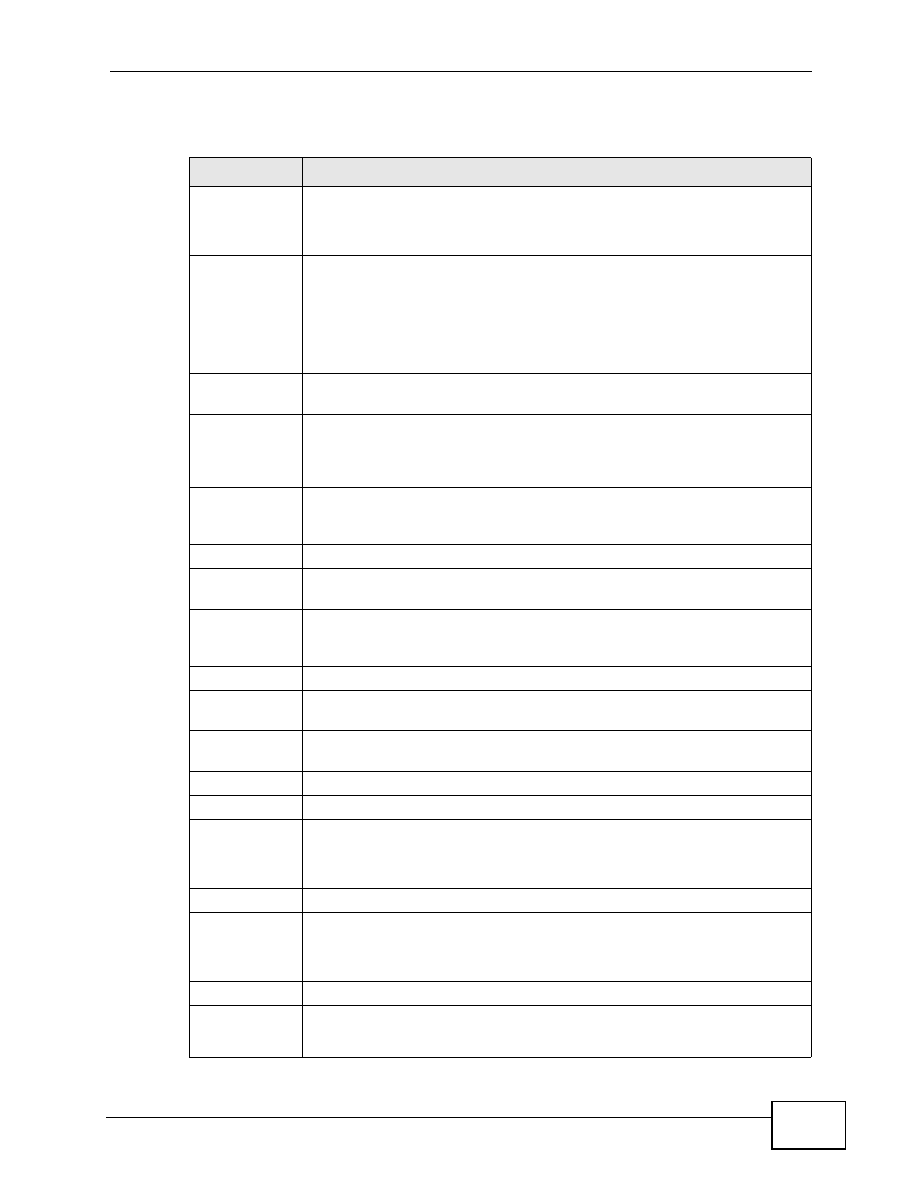
The following table describes the labels in this screen.
Table 84
Configuration > Captive Portal
LABEL
DESCRIPTION
Enable Captive
Portal
Select this turn on the captive portal feature.
Once enabled, all network traffic is blocked until a client authenticates
with the NXC through the specifically designated captive portal page.
Authentication
Method
Select an authentication method for the captive portal page. You can
configure the authentication method in the Configuration > Object >
Auth. Method screen (
This sets the default for all wireless clients interacting with the network
through the captive portal page. You can override this in the Auth.
Policy Edit screen (
Exceptional
Services
This table allows you to configure exceptions to the captive portal
interception of network traffic.
Add
Click to add a service that is allowed to by-pass the captive portal. This
allows certain networking features (such as being able to connect to a
DNS server, one of the pre-configured default exceptions), to remain
unhindered.
Remove
Select an exception from the table then click this button to remove it.
Once removed, all traffic from the specified protocol goes back to being
intercepted by the captive portal.
#
This is the index number of the Exceptional Services list entry.
Exceptional
Services
This column lists the services that you have flagged as exceptions to
captive portal interception.
Authentication
Policy
Summary
This table defines how captive portal interception is implemented using
the SSIDs, source IPs, and destination IPs that you specify.
Add
Click this to create a new entry.
Edit
Double-click an entry or select it and click Edit to open a screen where
you can modify the entry’s settings.
Remove
To remove an entry, select it and click Remove. The NXC confirms you
want to remove it before doing so.
Activate
To turn on an entry, select it and click Activate.
Inactivate
To turn off an entry, select it and click Inactivate.
Move
Click this to assign the selected policy a new Priority.
When you click the button, an entry box opens beside it. Enter the
priority value, then press [Enter].
Status
This indicates whether a policy is active or inactive.
Priority
This indictes the priority of a policy.
Priority values are unique to each policy. If you want to adjust the
priority, use the Move button.
SSID Profile
This indicates the SSID profile to which a policy belongs.
Source
This indicates the source IP address to be monitored by the policy.
All traffic from the source IP has the policy applied to it.