Chapter 33 System
NXC5200 User’s Guide
494
33.7.5 Examples of Secure Telnet Using SSH
This section shows two examples using a command interface and a graphical
interface SSH client program to remotely access the NXC. The configuration and
connection steps are similar for most SSH client programs. Refer to your SSH
client program user’s guide.
33.7.5.1 Example 1: Microsoft Windows
This section describes how to access the NXC using the Secure Shell Client
program.
1
Launch the SSH client and specify the connection information (IP address, port
number) for the NXC.
2
Configure the SSH client to accept connection using SSH version 1.
Remove
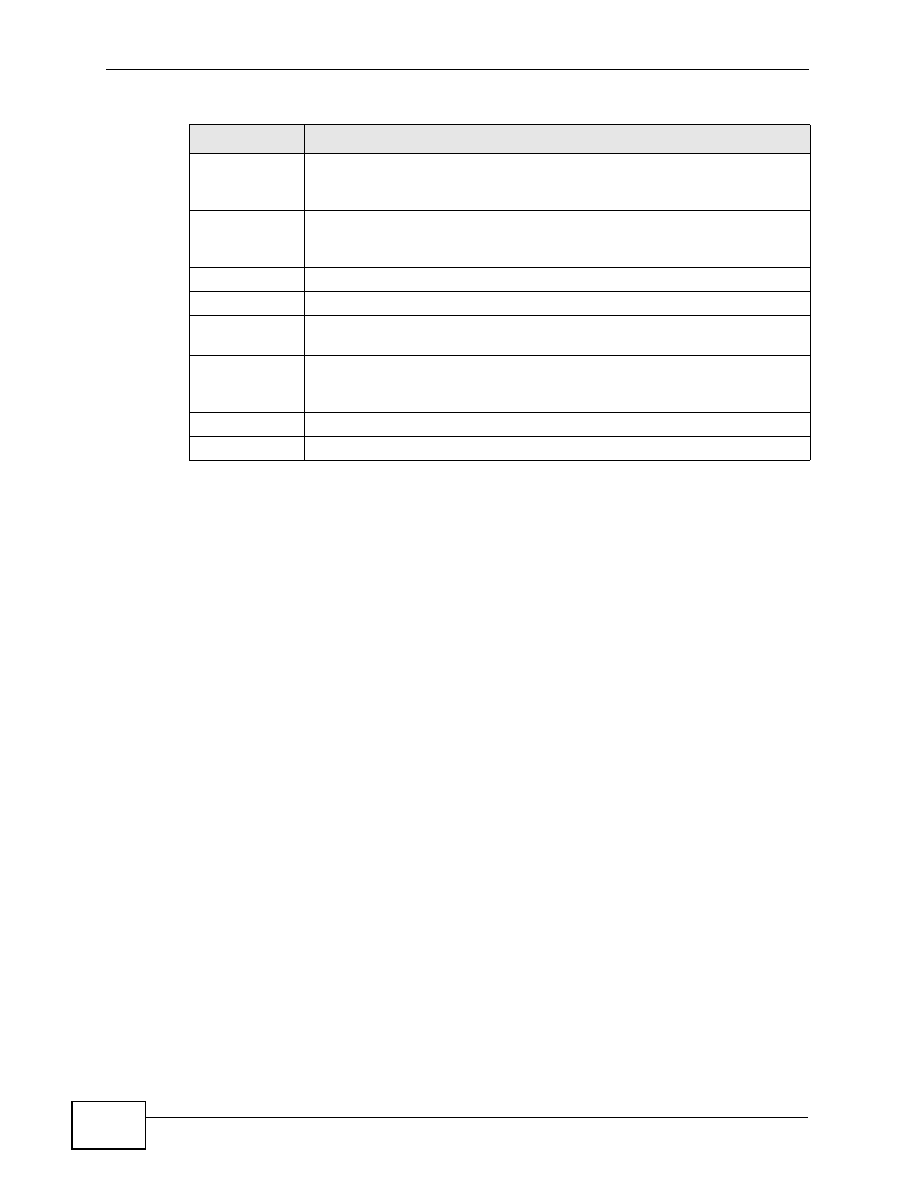
To remove an entry, select it and click Remove. The NXC confirms you
want to remove it before doing so. Note that subsequent entries move
up by one when you take this action.
Move
To change an entry’s position in the numbered list, select the method
and click Move to display a field to type a number for where you want to
put it and press [ENTER] to move the rule to the number that you typed.
#
This the index number of the service control rule.
Zone
This is the zone on the NXC the user is allowed or denied to access.
Address
This is the object name of the IP address(es) with which the computer is
allowed or denied to access.
Action
This displays whether the computer with the IP address specified above
can access the NXC zone(s) configured in the Zone field (Accept) or not
(Deny).
Apply
Click Apply to save your changes back to the NXC.
Reset
Click Reset to return the screen to its last-saved settings.
Table 186
Configuration > System > SSH (continued)
LABEL
DESCRIPTION