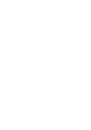
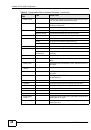
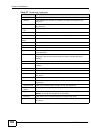
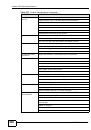
Index
NXC5200 User’s Guide
712
network-based intrusions
Nimda
Nmap
no IP options
non-RFC
characters
defined-char attack
HTTP-delimiter attack
O
object-based configuration
objects
AAA server
addresses and address groups
authentication method
certificates
for configuration
introduction to
schedules
services and service groups
users, user groups
obsolete-options attack
offset (patterns)
One-Time Password (OTP)
Online Certificate Status Protocol (OCSP)
vs CRL
OSI (Open System Interconnection)
OSI level-4
OSI level-7
other documentation
OTP (One-Time Password)
oversize
chunk-encoding attack
len attack
offset attack
request-uri-directory attack
P
P1
P2P (Peer-to-peer)
attacks
packet
inspection signatures
scan
statistics
padding
Pairwise Master Key (PMK)
payload
option
size
Peer-to-peer (P2P)
calls
managing
physical ports
and interfaces
packet statistics
,
PIN generator
pointer record
policy routes
actions
and address objects
and ALG
and interfaces
and schedules
and services
and user groups
,
,
,
,
and users
and VoIP pass through
bandwidth management
benefits
configuration overview
criteria
prerequisites
polymorphic virus
pop-up windows
port mapping
port scan, filtered
port scanning
port sweep
port triggering
and firewall
and policy routes
and service groups
and services
ports
Power LED
power off