Chapter 21 IDP
NXC5200 User’s Guide
333
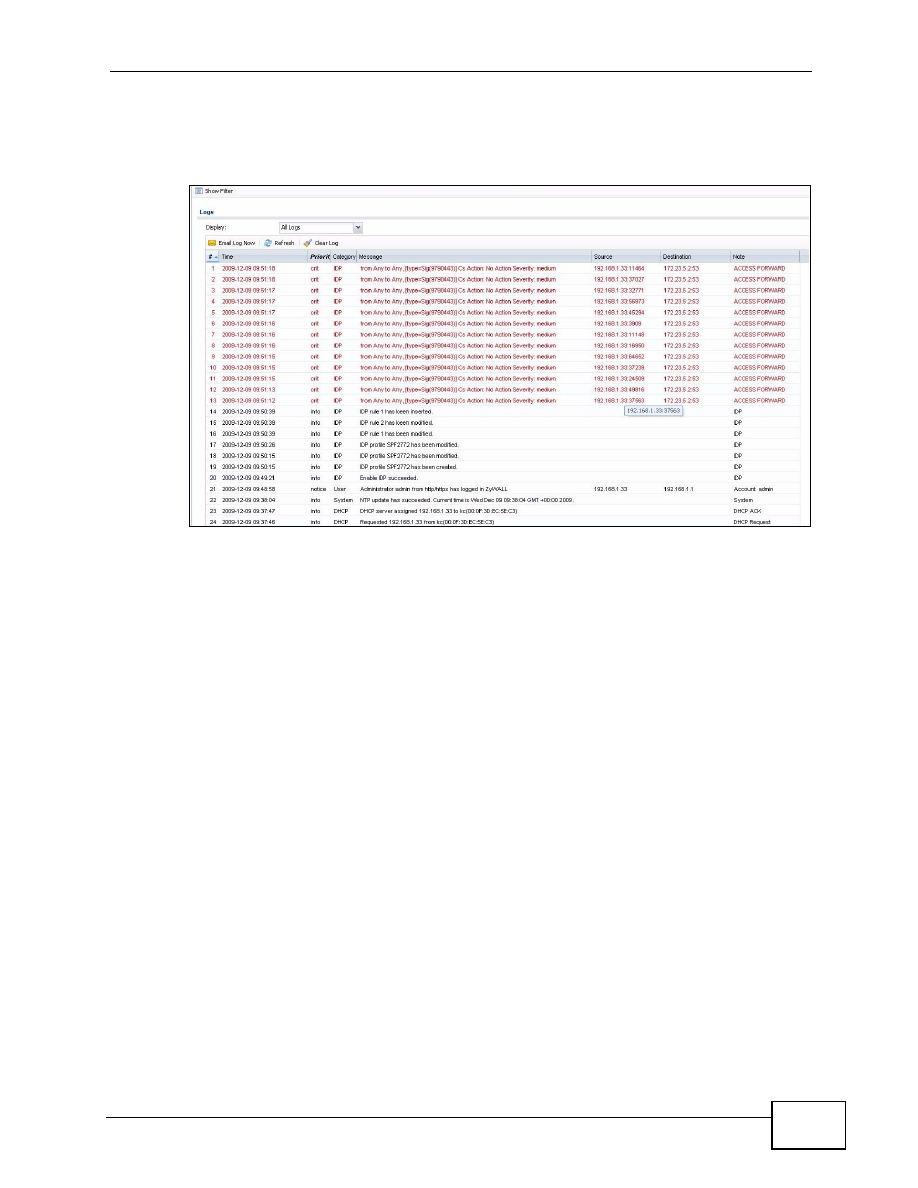
The destination port is the service port (53 for DNS in this case) that the attack
tries to exploit.
Figure 149
Custom Signature Log
21.8 Technical Reference
The following section contains additional technical information about the features
described in this chapter.
Host Intrusions
The goal of host-based intrusions is to infiltrate files on an individual computer or
server in with the goal of accessing confidential information or destroying
information on a computer.
You must install a host IDP directly on the system being protected. It works
closely with the operating system, monitoring and intercepting system calls to the
kernel or APIs in order to prevent attacks as well as log them.
Disadvantages of host IDPs are that you have to install them on each device (that
you want to protect) in your network and due to the necessarily tight integration
with the host operating system, future operating system upgrades could cause
problems.