Chapter 5 Tutorials
NXC5200 User’s Guide
93
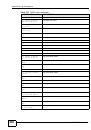
Here, an attacker sets up a rogue AP (RG) outside the network, which he uses in
an attempt to mimic an NXC-controlled SSID in order to capture passwords and
other information when authorized wireless clients mistakenly connect to it.
Figure 23
Rogue AP Example B
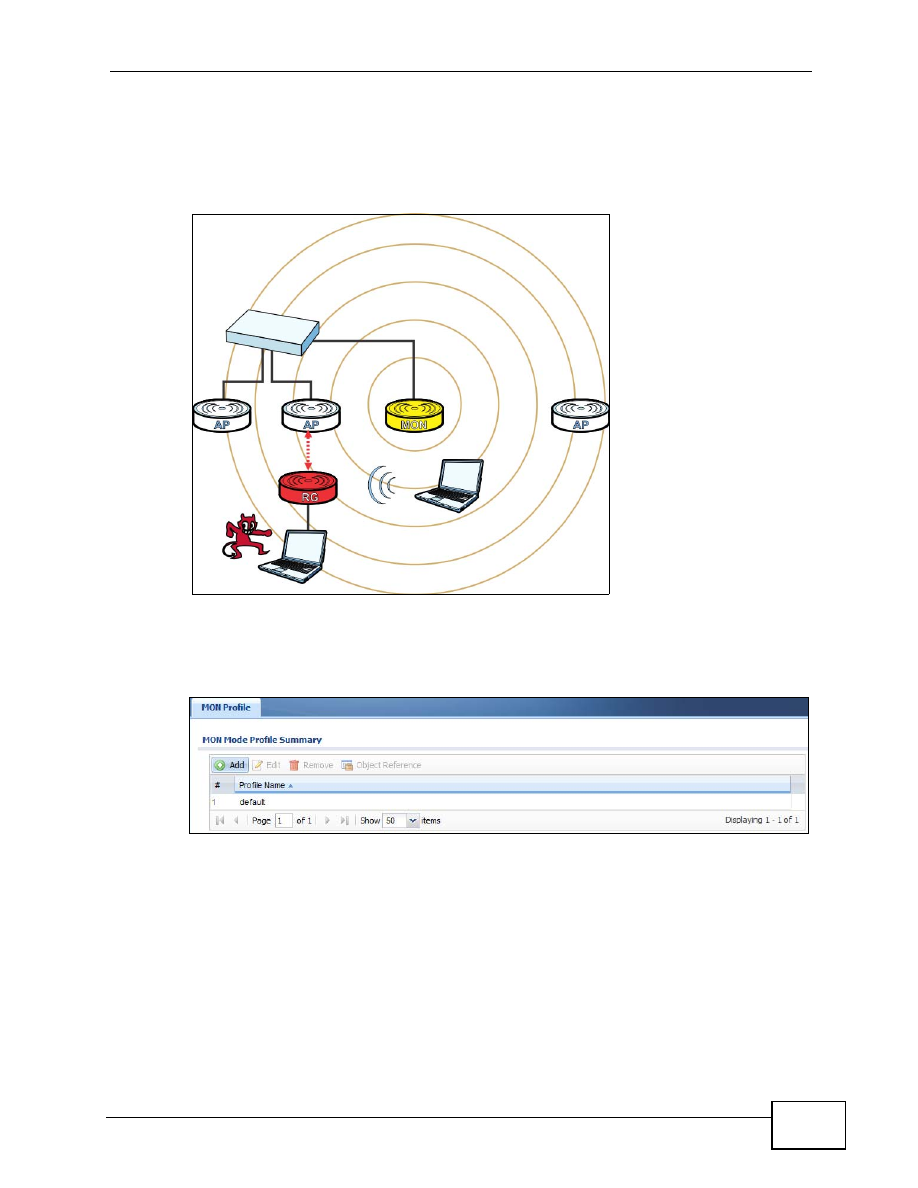
This tutorial shows you how to detect rogue APs on your network:
1
Click Configuration > Object > MON Profile.