Chapter 33 System
NXC5200 User’s Guide
491
unsecured network. In the following figure, computer A on the Internet uses SSH
to securely connect to the WAN port of the NXC for a management session.
Figure 226
SSH Communication Over the WAN Example
33.7.1 How SSH Works
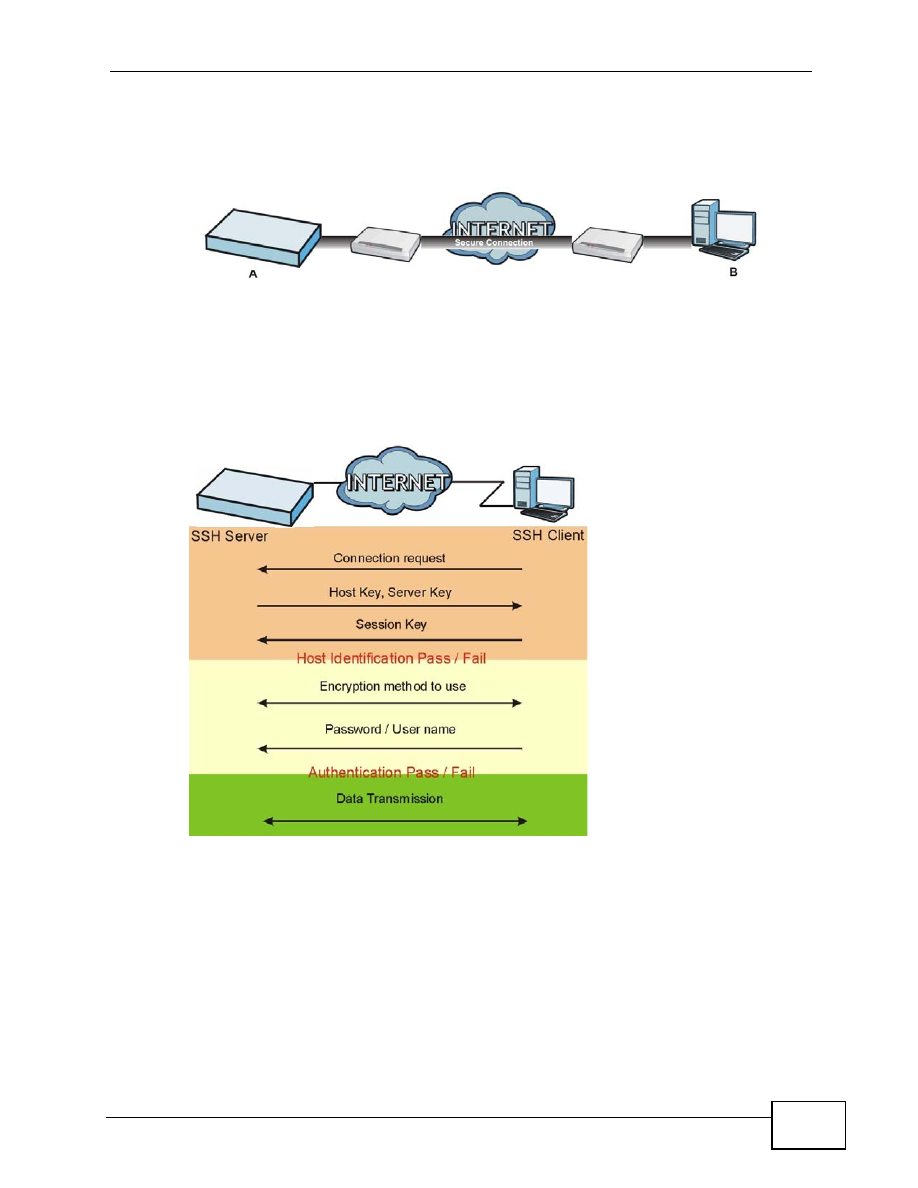
The following figure is an example of how a secure connection is established
between two remote hosts using SSH v1.
Figure 227
How SSH v1 Works Example
1
Host Identification
The SSH client sends a connection request to the SSH server. The server
identifies itself with a host key. The client encrypts a randomly generated
session key with the host key and server key and sends the result back to the
server.
The client automatically saves any new server public keys. In subsequent
connections, the server public key is checked against the saved version on the
client computer.