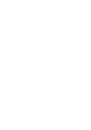
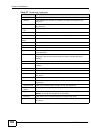
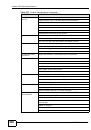
Index
NXC5200 User’s Guide
705
directory traversal
DoS/DDoS
double-encoding
false negatives
false positives
IIS-backslash-evasion
IIS-unicode-codepoint-encoding
IM
known
multi-slash-encoding
network-based
non-RFC-defined-char
non-RFC-HTTP-delimiter
obsolete-options
oversize-chunk-encoding
oversize-len
oversize-offset
oversize-request-uri-directory
P2P
pattern-based
scan
self-directory-traversal attack
severity of
spam
trapdoor
trojan
truncated-address-header
truncated-header
truncated-options
truncated-timestamp-header
TTCP-detected
types of
u-encoding
undersize-len
undersize-offset
UTF-8-encoding
virus
worm
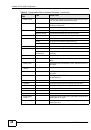
Authenex Strong Authentication System
(ASAS)
authentication
LDAP/AD
server
authentication method objects
and users
and WWW
create
where used
Authentication, Authorization, Accounting
authorization server
B
backdoor attacks
backing up configuration files
backslashes
bad-length-options attack
bandwidth
usage statistics
bandwidth management
and policy routes
behavior
configured rate effect
examples
in application patrol
interface’s bandwidth
maximize bandwidth usage
over allotment of bandwidth
priority
priority effect
see also application patrol
bare byte encoding
bare byte encoding attack
Base DN
base profiles
in ADP
in IDP
,
base36-encoding
base36-encoding attack
Basic Service Set, See BSS
Bind DN
BitTorrent
Blaster
boot module
boot sector virus
BSS
buffer overflow
buffer overflow attacks