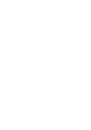
Index
NXC5200 User’s Guide
716
T
T/TCP
target market
TCP
ACK (acknowledgment)
ACK number
attack packet
connections
decoder
decoy portscan
distributed portscan
flag bits
port numbers
portscan
portsweep
RST
SYN (synchronize)
SYN flood
window size
Telnet
and address groups
and address objects
and zones
with SSH
Temporal Key Integrity Protocol (TKIP)
three-way handshake
time
time servers (default)
time to live
timestamp
token
traffic anomaly
traffic statistics
Transmission Control Protocol, see TCP
Transport Layer Security (TLS)
trapdoor attacks
trial subscription services
triangle routes
allowing through the firewall
vs virtual interfaces
trojan attacks
troubleshooting
truncated-address-header attack
truncated-header attack
truncated-options attack
truncated-timestamp-header attack
Trusted Certificates, see also certificates
TTCP-detected attack
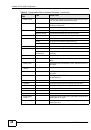
U
UDP
attack packet
decoder
decoy portscan
distributed portscan
flood attack
messages
port numbers
portscan
portsweep
u-encoding attack
undersize-len attack
undersize-offset attack
unreachables (ICMP)
update
configuration overview
prerequisites
updating
anti-virus signatures
IDP and application patrol signatures
signatures
system protect signatures
upgrading
firmware
licenses
uploading
configuration files
firmware
shell scripts
URI (Uniform Resource Identifier)
usage
CPU
flash
memory
,
onboard flash
sessions
,
user authentication
external
local user database
user awareness